Instant messaging is not a new concept; in fact, instant messaging software has been around for over 20 years in many different forms. A more popular method of instant messaging these days is done with the use of the software known as Skype. Skype allows for more than just text chatting but also calling a person and engaging in video chat. Therefore, it is no surprise that Skype is just another avenue for cyber-criminals to try and infect users using another age-old concept, social engineering.
Skype Infections of the past
The Skype method of malware spreading isn’t new either, we can look back to earlier this year and the infection of Syrian rebels with BlackShades and Dark Comet RATs. The main method of spreading was using compromised Skype accounts to spread links to a fake a YouTube page that downloaded the malware masked as a Flash update.
This new series of infections follows a similar principal in that a specialized piece of software takes over the users Skype account and uses it to spread malicious links to the contacts of the infected user. We will go over how this is accomplished and how to protect your system from it in the next sections.
Infection Method
As I mentioned, using Skype to send malware is no new trick, however the method in which it is done is strangely effective. I believe it lies in the wording and all of our own selfish concerns about how we appear to other people. The Skype message looks something like this:
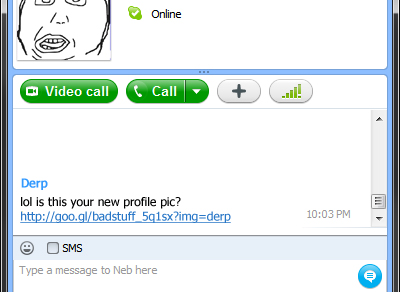
So in short, you get a private message from one of your contacts and it says “lol is this your new profile pic? ” and immediately you might begin to panic that somehow an embarrassing picture of you has been set as your Skype profile picture. You have no choice but to click the link to either confirm or deny that what your friend is referencing is in fact your picture. However, once you do click it, you are directed to a download for a ZIP file, which you assume is the picture, you download it, open the file and double click the file only to discover that it vanishes and now you are most likely infected with something bad. After the initial infection, the malware hijacks your Skype session and sends out the same message to all of your contacts, now possibly infecting all of your friends and family. Here is a comic explaining everything in highly technical detail:
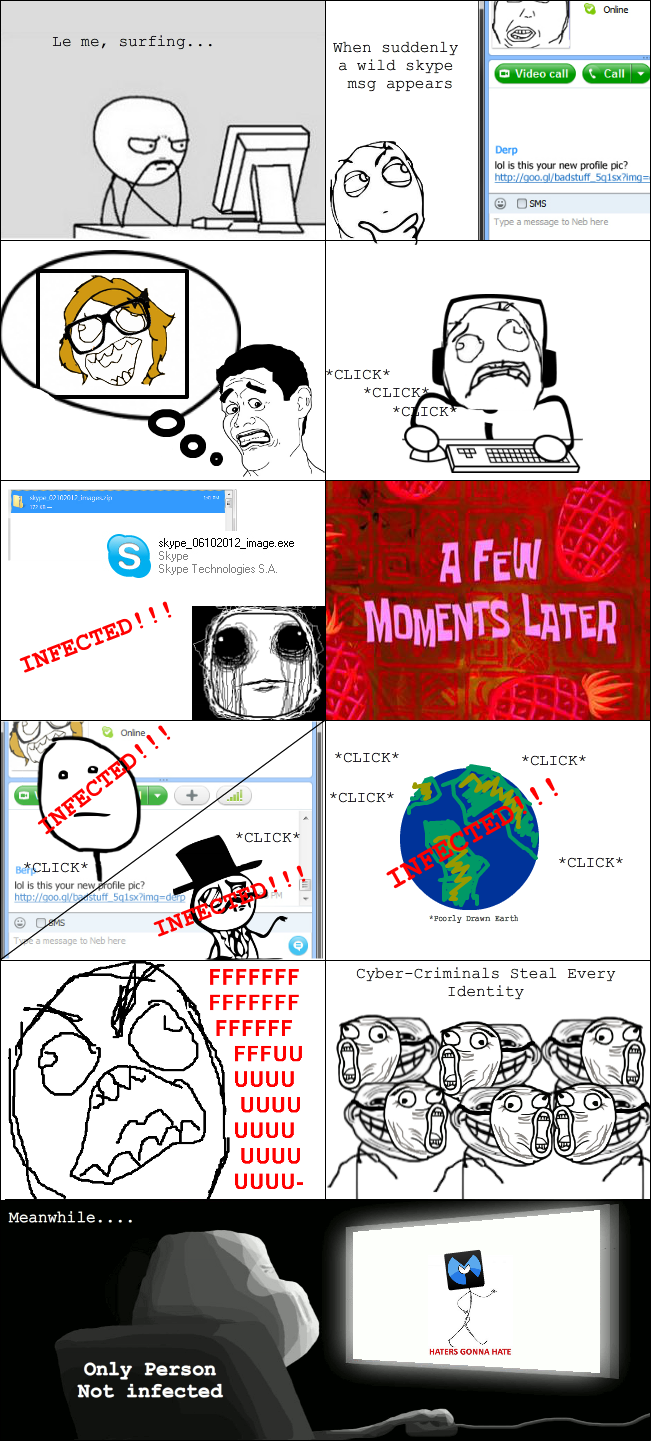
Malware Information
The malware being spread is a variant of the DorkBot worm which has been around for a little while and notably seen last year being spread via Facebook chat. An interesting coincidence considering that it is possible to communicate with your Facebook chat friends via Skype. In essence, this infection might spread beyond just Skype when Facebook users begin to see the links as well.
DorkBot is a type of botnet malware that infects the system by using persistent mechanisms and takes commands from a remote C&C server. Here is a list of some of the functionality DorkBot can execute on an infected system:
- Steal Login Data from numerous visited sites
- Interfere with DNS resolution (redirect you)
- Execute 3 different types of Distributed Denial of Service Attack
- Act as a proxy server for other malware or hackers to pipe traffic through
- Install subsequent malware downloaded at the request of the C&C
- In some cases, it has been reported that DorkBot can even install Ransomware that locks down the system and demands a ransom of $200.
Also, if you think that this type of attack threatens only Skype users, think again because DorkBot is also known to infect and spread propagating messages through other instant messaging applications like:
- MSN Messenger
- Windows Live Communicator
- Pigeon
- mIRC
- xChat
By monitoring the internet surfing of the user, DorkBot will check for certain keywords located in the URL of the site the user is visiting, this is so it knows when to conduct its data stealing operation. Some of the sites that DorkBot checks for (and therefore steals from) are:
- Yahoo Mail
- Netflix
- PayPal
- Runescape
- Steam
- Many more…
It also likes to block the websites of various Anti-Malware/antivirus companies including Malwarebytes, Avast, Norton, Kaspersky and many others. The security company Trend Micro created a really nice entry in their malware encyclopedia on the functionality of DorkBot; it includes a listing of all the different sites and types of info that the malware steals, if you want to know more about how DorkBot works and the threat it poses check out :
Threat Encyclopedia: WORM_DORKBOT
Protection Practices
As mentioned earlier, the effectiveness of the spreading methods used by DorkBot (i.e. Skype) have been strangely effective and as a result, the amount of infected systems have grown substantially in a short amount of time. However, could this kind of attack be avoided for the future? Should we ever trust the links that our friends send us, especially if it is about us? The answer is no, you should not trust anything on your computer. A small amount of paranoia and prudent practices can go a long way in keeping your system safe.
In this case, Malwarebytes Anti-Malware and other types of security software have done a good job at being able to detect, prevent and remove DorkBot malware from infecting systems in a short amount of time. However, this might not always be the case and it should be a lesson to all of us to keep our security software updated and be weary of any link we click or file we open if we are not 100% positive of the source and destination.
Conclusion
This method of infection is just one of many other examples of how attackers, hackers, scammers and other cyber-criminals are using non-standard mixes of social engineering, phishing and malware spreading to steal your personal information, take over your system and extort money and livelihood from you and your family. It is also foolish to think that this kind of attack will ever go away, it is incredibly effective and it relies on the one thing that no security software can protect you from, human nature. For more information on traditional phishing attacks and modern attacks using non-standard methods, check out my blog series from a few months back: Phishing 101.
References:
Adam Kujawa is a computer scientist with over eight years’ experience in reverse engineering and malware analysis. He has worked at a number of United States federal and defense agencies, helping these organizations reverse engineer malware and develop defense and mitigation techniques. Adam has also previously taught malware analysis and reverse engineering to personnel in both the government and private sectors. He is currently the Malware Intelligence Lead for the Malwarebytes Corporation. Follow him on Twitter @Kujman5000