…because some malware is too heinous for clever puns.
Ransom software or Ransomware, takes advantage of our constant need for information, communication and entertainment by hijacking our computer systems and demanding payment for returned use. It hides under the masks of government agencies and uses tactics similar to criminal interrogations to guilt the user into blindly paying fines to hide their assumed shame. Anyone and everyone are susceptible to its malicious trickery and the worst part is it is not always so easy to remove. This blog post is going to shed light on what Ransomware really is and most importantly, how to get rid of it. Ransomware is holding your system hostage and you should never negotiate with cyber-kidnappers.
What is Ransomware?
While a little late for Halloween, Ransomware likes to play dress up and it’s favorite costume is a government agency. Modern Ransomware hijacks the users system by preventing any use of applications or even access to the operating system itself. Instead, it only shows a single screen claiming to be a notice from a government law-enforcement agency and fining the user for illegal activity performed on the system.
The above screenshot is an example of Ransomware claiming to be a government entity. To add to the ruse, it will use the official seal of the agency, hijack the users webcam to get a picture or video of them and then list out numerous laws that the user has possibly broken that resulted in their being fined. In addition, it offers an input area to pay the fine by entering the number of an untraceable pre-paid card you can purchase at one of the fine locations on the right side of the screen.
The laws that the user is accused of breaking include:
- Copyright Infringement
- Pornography
- Child Pornography
- Promoting Terrorism
- The system was infected with malware and infected other systems with malware
- Gambling
The list includes some fierce accusations of illegal activity and then some not-so-fierce and not-so-illegal things too. Legal or not, millions of people can say they have used their computer to look at pornography, download entertainment files and played online gambling games. However, other users might have a hard time understanding not only what these accusations include but also if they are not already guilty of them. It is safe to say that this scheme pry’s on the guilt and paranoia of the average user and if this is your first time hearing about this malware, it might seem silly that anyone would really fall for it. Fact is, a lot of people fall for it. According to a report done by Symantec, this particular style of malware and extortion earns cyber-criminals around $400,000 a month!
On a side note, the only fake crime that is 100% applicable to every user on that list is the one about malware.
How many people reading this blog post can say they are 100% certain that they have never been involved in Child Pornography, Copyright Infringement or Promoting Terrorism? I imagine most can. However, start looking at it from a broad point of view. What if while searching for something completely different, you came across child pornography, I am sorry if that has ever happened to you but could it be considered breaking the law if you had? What about a song you downloaded off the internet that was hosted free on a website or maybe you got a copy of it from a friend, were you breaking copyright infringement by doing that? Finally, have you ever decided to post your opinion about how the government is being run, do you support the Occupy movement or the group Anonymous in anyway? Could it be considered ‘promoting terrorism’ by speaking up against the government?
Fact is most people, when left to their own nervousness and paranoid when being pressured by a government agency, might assume guilt for things they did that were not illegal. It all comes down to how each individual person perceives it. This might seem like a small amount of guilt but in reality, it is strong enough to make even a very security conscious and well-mannered person pay these Ransomware fines to make their guilt go away. This natural human response has made this attack method very popular among cyber-criminals and the ironic part is that it’s the same tactics used when law enforcement officials solve crimes and find the bad guys.
How can you protect against it?
Protection from Ransomware is the same as protection from any malware:
- Keep your operating system/browser/plug-ins up-to-date with patches and updates
- Use an antivirus AND anti-malware solution on your system
- Employ the use of safe surfing practices to reduce the risk of drive-by attacks
- Keep up to date system restore points (makes it easy to remove malware if you just revert to an earlier, malware-free, state)
In addition to the above measures, installing an advertisement-blocking tool like AdBlock Plus for your web browser or HostsMan for your entire operating system can block malicious advertisements or pop-ups that expose your system to drive-by exploit attacks. One of the most commonly seen ways in which Ransomware spreads is by using browser exploit kits hosted on sites that fake advertisements and social engineering tactics lead users to, and results in malware being downloaded and executed on the system outside of the user’s knowledge.
How can you remove it?
Because there are varying levels of infection depth when it comes to Ransomware (some harder to remove than others) I am going to go through how to remove the most intrusive type of Ransomware from your system. By most intrusive I mean Ransomware that has disabled the ability to start the system in “Safe Mode” and you have no way to perform a system-restore or obtain enough access to the operating system to download/run anti-malware software.
- Obtain a Kaspersky Rescue Disk
- You can get this by using an uninfected system to perform an internet search for the disks image (ISO) and burn it to a CD or copy it to a USB drive that has at least 8 GB available on it. If you don’t know how to do this, check out this link: Malwarebytes Tutorial on Making A Kaspersky Rescue Disk
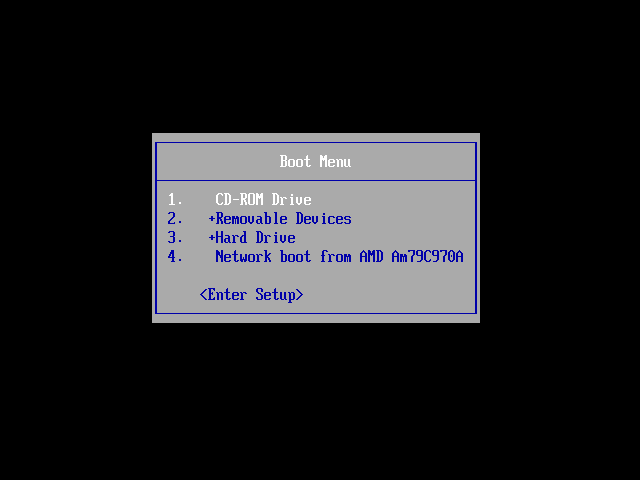
- Boot the rescue disk rather than your own operating system by either modifying your BIOS boot order or selecting from a boot menu. (Depending on your Operating System, hit F8 or F7 before the Windows Logo pops up)
- Once it begins booting, you should see the Kaspersky Rescue Disk interface show up asking for input to continue booting the rescue disk interface.

- After you select your language and agree to the Kaspersky use agreement, you will be given numerous options as to how to proceed. I recommend using the graphical interface for the recovery console since it is easy to understand and use. For more advanced users you can use the command line if you like, it allows you to customize your scans and have greater control over how the recovery process works. In addition, I had difficulty using my mouse when I ran the rescue disk in my VM and therefore the command line option was preferable.

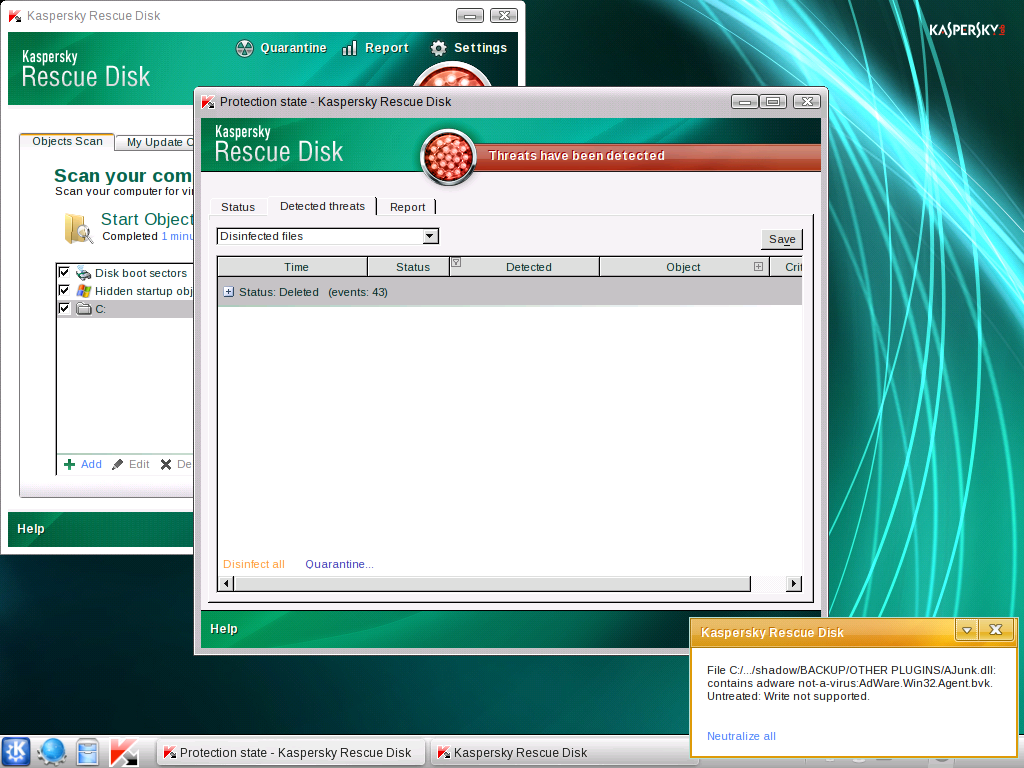
- Once the graphical interface finishes starting up, the recovery disk should automatically open the Rescue Disk scanner interface.

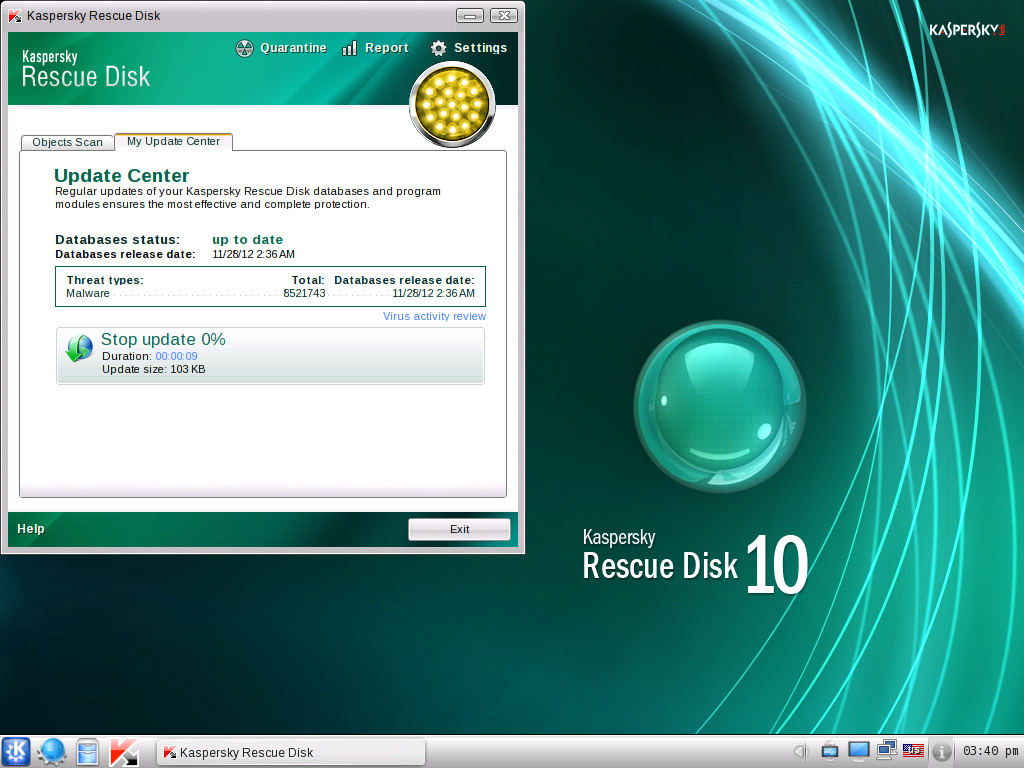
- To ensure that the rescue disk has the best chance of detecting and removing enough of the malware to give you access to your system again, click on the “My Update Center” tab to update the scanners definitions to their most current release.
- Once the scanner is up-to-date, go back to the “Objects Scan” tab. I recommend selecting all objects (all system drives/disk boot sectors/hidden startup objects) just to be thorough. Once done go ahead and click on the “Start Objects Scan” button.
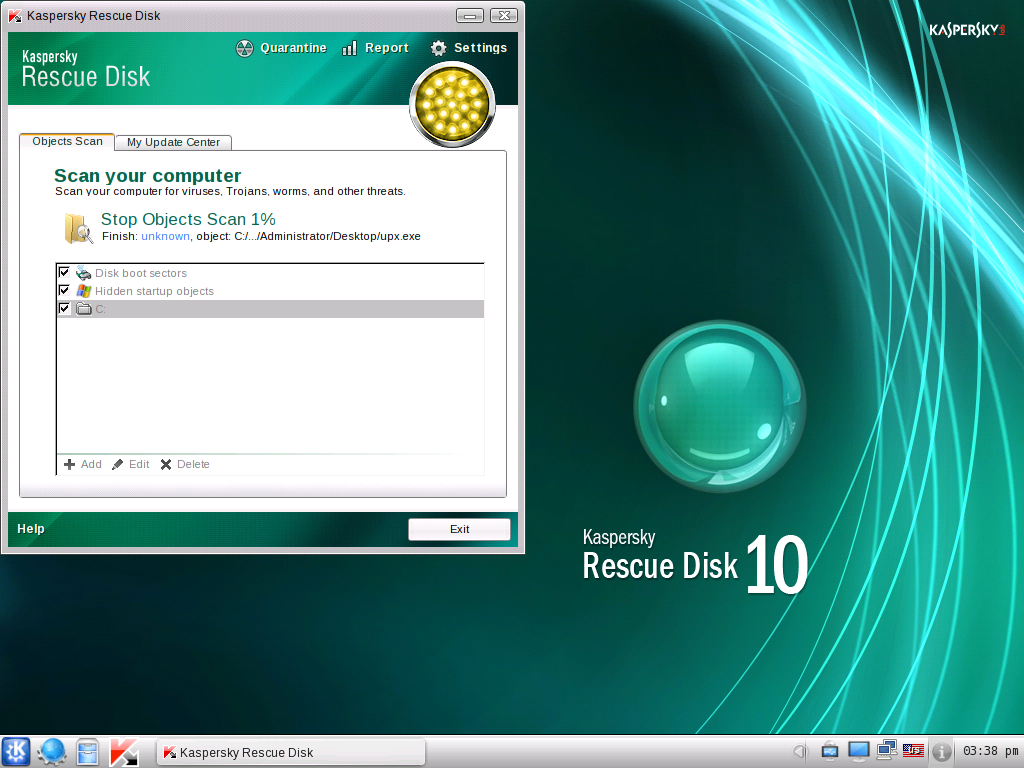
- Once the scan is complete, follow the directions to disinfect your system of all detected malware and restart your system. Make sure you revert if you made any changes to the BIOS, so you boot from your Hard Disk again.
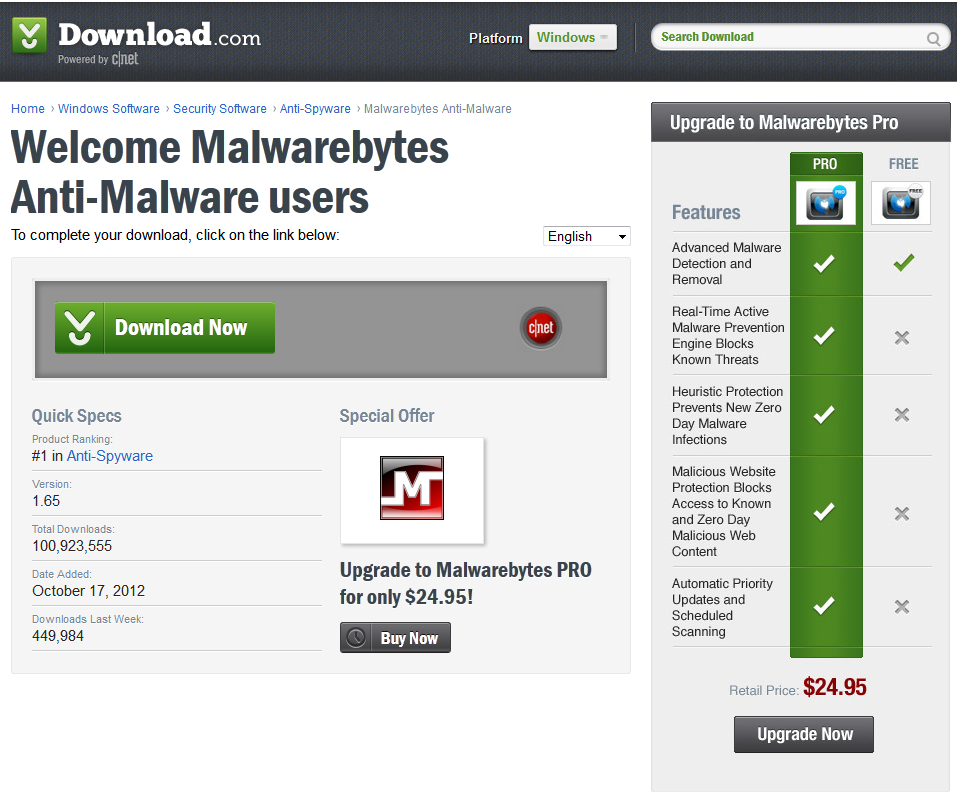
- If your system boots correctly, open your browser, download the free version of Malwarebytes Anti-Malware, and do a full scan to make sure that you catch any other malware that might be lingering.
- In addition, you should run a scan with other antivirus/anti-malware solution as well to be doubly sure that you caught everything.
At this point, hopefully you have gained control of your system again and if so, congratulations! However, this solution is meant for the most intense and difficult to remove examples of Ransomware, most are much easier to remove. Be sure to try the following solutions before going as far as the above tutorial describes:
- See if you can access your system by rebooting in Safe Mode with Networking, if you can see if you are able to download an antivirus or anti-malware solution and run a scan.
- If you cannot access any antivirus or anti-malware websites to download additional software, you might have to copy the software onto your system by using a “live” disk for either Linux or Windows. Once you copy the software over, you can boot into Safe Mode with Command Prompt and using the command console, install the software and scan the system.
- If you have been making regular backups with Windows System Restore and have a boot disk for your operating system, try booting it (just as with Kaspersky Rescue Disk) and try reverting your system to a previously saved restore point. Once done, make sure that you run an in-depth antivirus and anti-malware scan to ensure that the image has not previously been infected with malware.
If none of these options work or are not possible for your situation, it might be a good idea to obtain the services of a professional to try to remove the malware. You can sign up to the Malwarebytes Forums and ask one of our experts to help you remove the threat from your system. Although, whatever you do, DO NOT pay the fine.
Conclusion
Ransomware is fierce, smart and dangerous. As we continue to watch its evolution unfold and numerous users becoming victims of its extorting ways, we see more and more lethal functionality. Ransomware now employs the use of rootkit technology and even modifies the user’s ability to boot in safe mode. It is because of these constant upgrades that I have described a method to remove the malware from outside of the operating system and, hopefully, it will continue to remove the threats before any more victims can pay their fines and lose their hard-earned cash. However, the best weapon against Ransomware or any malware for that matter is education. By learning about the threat, learning how to stop it and spreading the knowledge to friends, family, colleague and even perfect strangers, you are making a dent in the pockets of the cyber-criminal organizations. Thanks for reading and safe surfing!
References
- http://www.symantec.com/connect/blogs/ransomware-how-earn-33000-daily
- http://support.kaspersky.com/viruses/rescuedisk
—————————————————————————————————————————–