During the course of your life, there are many times when you have to prove who you are. Whether it’s applying for a loan, getting your driver’s license, or signing into your email account, a process has to occur to “authenticate” your identity. Otherwise, anybody could be you.
In the 21st century, we’ve seen a sharp increase in Identity Theft, a term you’ve probably heard a lot in the media. The idea of pretending to be someone you’re not is nothing new, but in the digital era, fooling a computer is a little easier than your bank teller. The problem has become so prevalent that companies have emerged dedicated solely to fighting identify theft related crimes.

Companies like LifeLock had emerged amidst the increasing amount of Identity Theft.
When it comes to your digital life, passwords hold the keys. While new technology emerges like biometric scanners and smart cards, the password is still the most commonly used form of authentication since it is both cheap and easy to implement. Over the years, you’ve probably used a password for virtually all of your online accounts, from your Facebook account, your personal email, and even your bank account (and probably the same password for all of them).
Considering this, it’s no surprise that, since your passwords are so valuable, they’re highly targeted by hackers and malware. News reports develop almost daily of security breaches where passwords are stolen from private database—just a few days ago, in fact, the co-founder of the infamous “Pirate Bay” bit torrent site was charged with hacking crimes in Sweden, where personal data was stolen from several companies.
In addition, programs like keyloggers are often packaged into much of today’s modern malware to record a user’s keystrokes while using a computer, often for the purpose of obtaining passwords. With the danger of drive-by downloads, this kind of malware could be installed to your computer without your prior knowledge or consent. What’s more, there are several password “cracking” programs in existence that use several techniques to brute-force weak passwords.
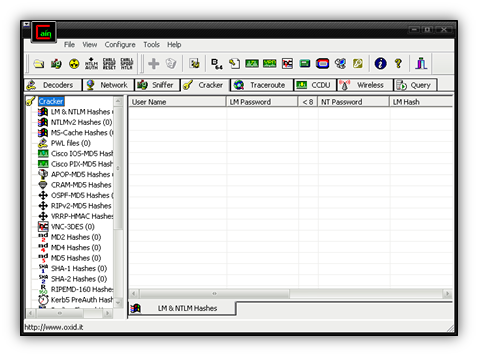
Cain & Abel, a popular password cracking tool.
So what can you, the user, do to protect yourself? This blog post will talk about password security from all angles, and give you the best tips at protecting your private information.
Step 1: Use a strong password You’ve probably tried to register an account online before and had the system return with a message that your password isn’t strong enough or doesn’t meet the complexity requirements. You then might have become frustrated and added “123!” to the end of what you had. I know I’m guilty of this.
The problem most of us run into is we can’t remember these convoluted passwords. In fact, some of us resort to keyboard patterns or familiar movie names to help us remember, but that isn’t really going to make your password any “stronger” as it’s vulnerable to shoulder-surfing (someone else watching) and password tables often guess them.
Creating a strong password can seem difficult at first but there are tools available to make it easier. For instance, go to http://howsecureismypassword.net/ and type in a password you might consider using (don’t worry, it’s safe). If your password can be cracked instantly or in a short amount of time, it may be time to change it to something more complex. Try to remember the following when creating your password:









