Just recently, a fellow researcher here at Malwarebytes received an email asking us to stop blocking their website.
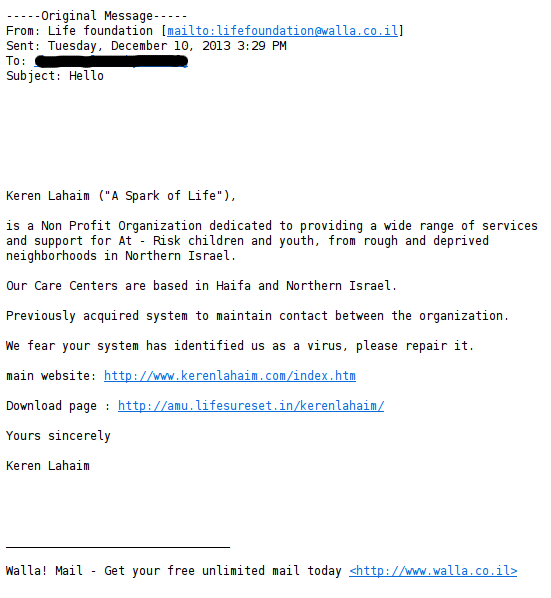
The link navigates to a website supposedly advertising an Israeli charity, all text appears in Hebrew.
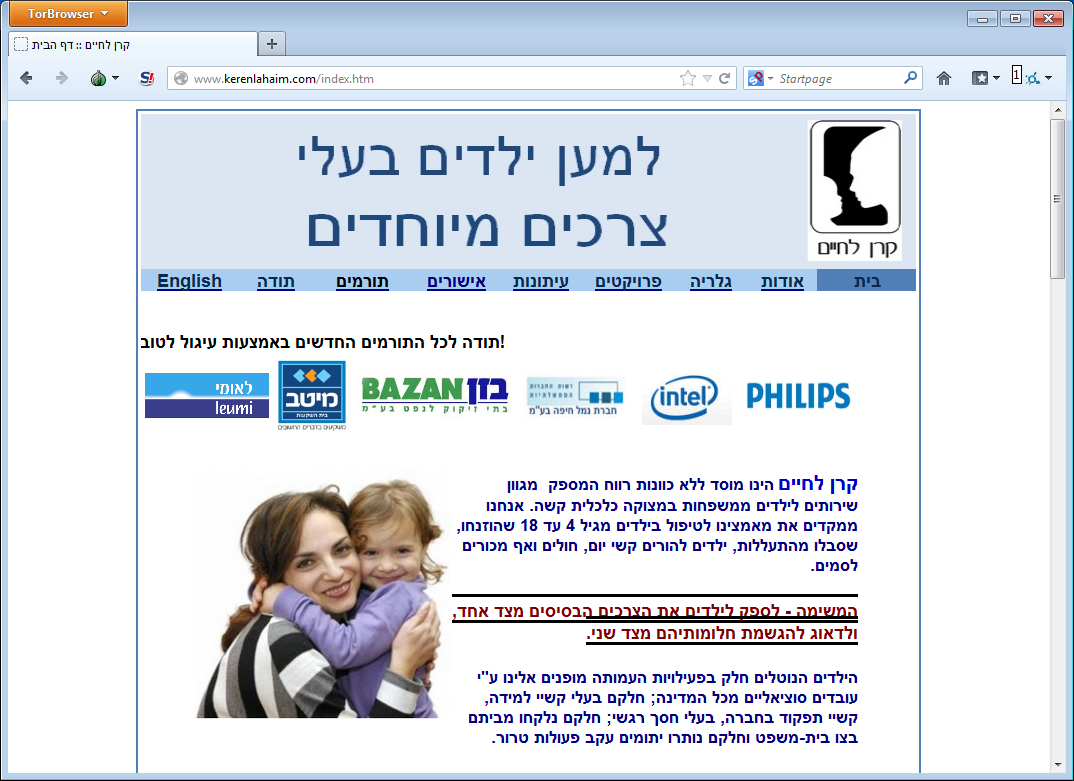
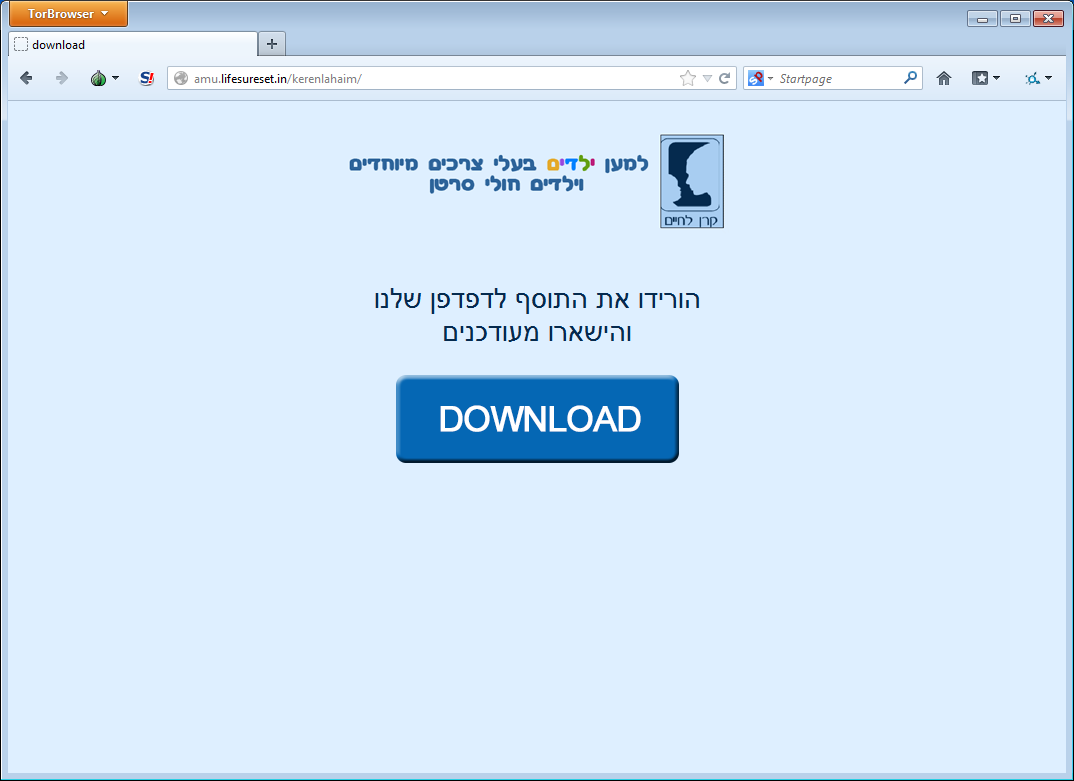
The download link mentioned in the e-mail is also on this page, and translates to “Want to remain updated all the time? Join us.” Below is a picture of the download page that says “Download our browser extension and stay updated.”
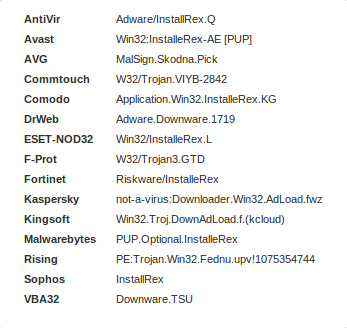
The downloaded file called ‘Keren.exe’ and is detected by 15 vendors on Virustotal (report found here). Malwarebytes detects the program known as “InstalleRex” as PUP.Optional.InstalleRex.
WebPick Internet Holdings Ltd., a company based in Ramat Ha’Chayal Tel Aviv, Israel, as per their LinkedIn page found here, created InstalleRex.
InstalleRex also has its own website at https://www.installerex.com/#! and marketed as “The Cloud Based Installer”. The front page of their website reads:
“InstalleRex is a unique, smart, cloud based installer, customized to your needs.”
When we run Keren.exe, we get the following dialog:
Furthermore, when viewing the End-User License Agreement (EULA), we see it’s presented by JustplugIt Ltd. A little research shows that JustplugIt is a service by Web Pick that offers a “cross-platform development platform that is beneficial to aspiring developers.”
A recent blog post by Justplugit suggests there is some suspicion around the service, stating that “For the most part the negative publicity about this awesome web service is mostly unsubstantiated lies and rumors.” After a little more investigating, we find out why that could be.
When taking a closer look at the EULA, there are some interesting snippets found, particularly about data collection the software makes (you can read the full EULA here):
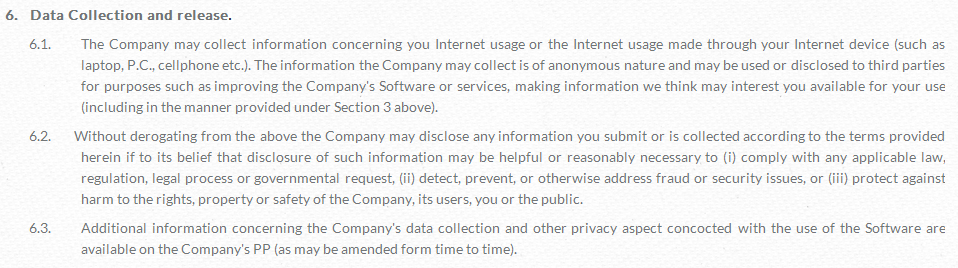
Some lines here include “The Company may collect information concerning you (your) Internet usage or the Internet usage made through your device” as well as “the Company may disclose any information you submit or is collected according to the terms provided herein”.
With that in mind, it seems fair to say the software collects information about you and gives it away. InstalleRex is classified by many vendors as adware for this reason.
However, the problem is that you may never know it, since most people don’t actually read EULAs before clicking ‘Next’ (I’m guilty myself). This allows shady companies like WebPick to legally collect and sell information to others, since users have to accept the EULA.
As for Keren.exe, the installed chrome extension is downloaded to a randomly named folder, and merely directs users to several different charity websites.
For a list of all the junk that InstalleRex brings with the toolbar, see the regshot capture below.
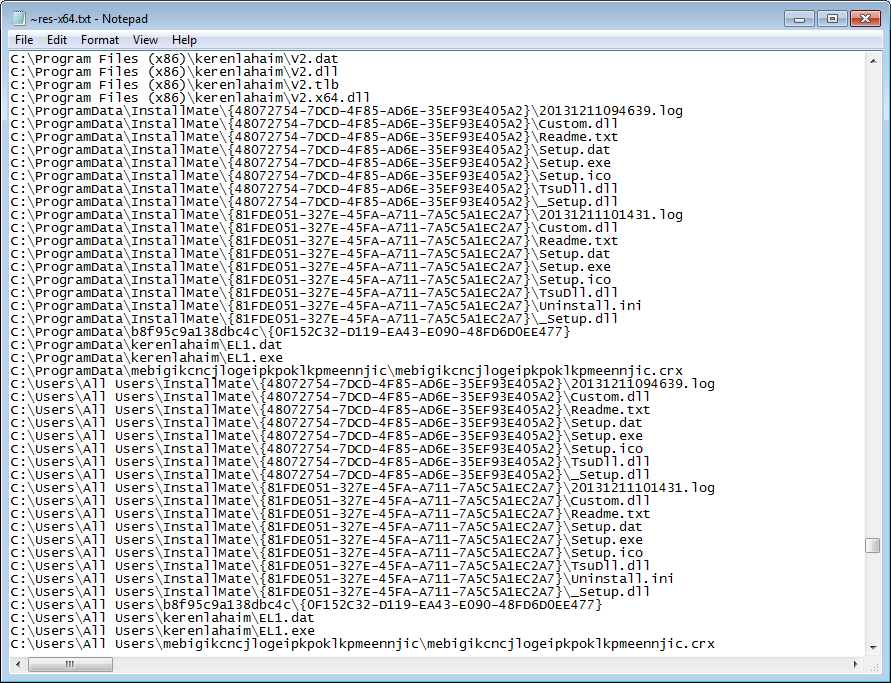
Amongst the files dropped and executed include EL1.exe and v2.dll, which is the CRXDrop/MegaSearch Adware (virustotal report here). Malwarebytes detects this file as PUP.Optional.CRXDrop.A. This program is known to hook into a user’s web browser and collect information for other targeted advertisements.
It’s important to remind our readers that these programs are technically not malware; however, they are still not recommended because they collect your information for advertisements to make money for themselves and their partners (they gain, and you lose).
In addition, the scope of this collection can change, and they aren’t obligated to inform you about it. For these reasons, Malwarebytes recommends users stay away from the InstalleRex installer as well as other PUPs (for our blog on the Malwarebytes PUP policy, click here).
Added thanks to Steven Burn for research material.
_________________________________________________________________
Joshua Cannell is a Malware Intelligence Analyst at Malwarebytes where he performs research and in-depth analysis on current malware threats. He has over 5 years of experience working with US defense intelligence agencies where he analyzed malware and developed defense strategies through reverse engineering techniques. His articles on the Unpacked blog feature the latest news in malware as well as full-length technical analysis. Follow him on Twitter @joshcannell










