Hackers: They’ll turn your computer into a BOMB! “Hackers turning computers into bombs” is a now legendary headline, taken from the…
Tag: hackers
Misleading cybersecurity lessons from pop culture: how Hollywood teaches to hack
In pop culture, cybercrimes are often portrayed as mysterious and unrealistic. Hackers are enigmatic and have extraordinary tech abilities. They can…
15,000 webcams vulnerable to attack: how to protect against webcam hacking
Webcams may have been around for a long time, but that doesn’t mean we know what we’re doing with them. Webcam…
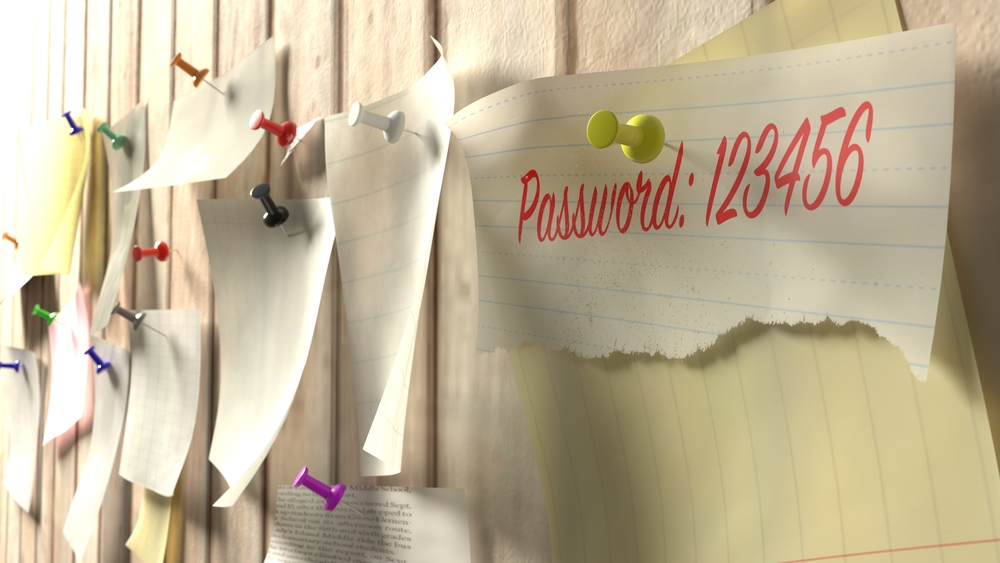
Are hackers gonna hack anymore? Not if we keep reusing passwords
Enterprises have a password problem, and it’s one that is making the work of hackers a lot easier. From credential stuffing…
How to browse the Internet safely at work
This Safer Internet Day, we teamed up with ethical hacking and web application security company Detectify to provide security tips for both…
A week in security (January 7 – 13)
Last week on the Malwarebytes Labs blog, we took a look at the Ryuk ransomware attack causing trouble over the holidays,…
Under the hoodie: why money, power, and ego drive hackers to cybercrime
Just one more hour behind the hot grill flipping burgers, and Derek* could call it a day. Under his musty hat,…
Did my comment on your blog get lost?
If you ever feel bad about your job because of mindless tasks you must perform day after day, or if you’re…
UK law enforcement: an uphill struggle to fight hackers
About 16 years ago in the UK, I walked into a local police station to report a computer crime, because walking…
How we can stop the New Mafia’s digital footprint from spreading in 2018
Cybercriminals are the New Mafia of today’s world. This new generation of hackers are like traditional Mafia organizations, not just in…