These days it is getting harder and harder to download a program from its official source, in its original format, without additional pieces…
Tag: Jerome Segura
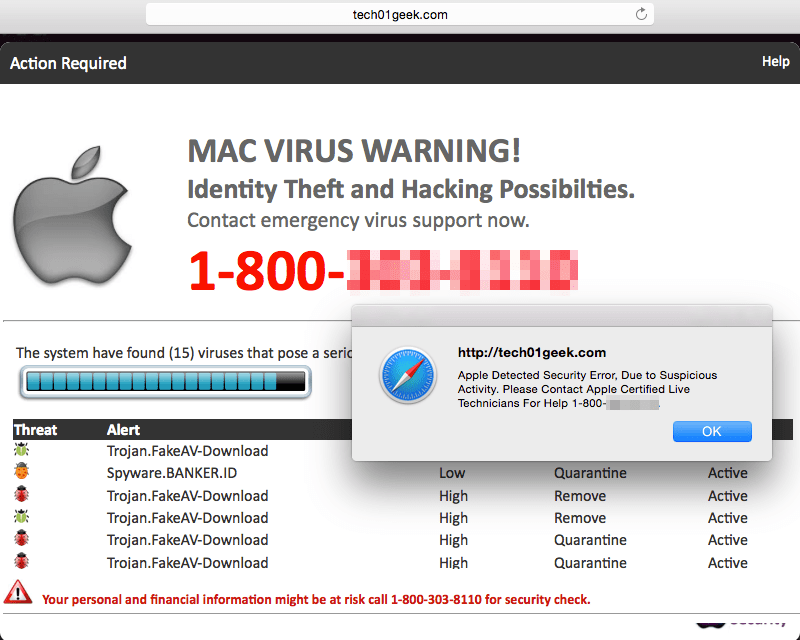
Mac users: Beware of increased tech support scam pop-ups
Last month, we warned you about a rise in tech support scam pop-ups primarily affecting Windows where severe virus warnings often…
AskMen.com compromised again
Last month, security firm Websense reported that popular website AskMen.com was compromised to serve malicious code. Today, our honeypot captured an attack…
A cunning way to deliver malware
Potentially unwanted programs, also known as PUPs, continue to be a real nuisance. A recent blog post by Will Dormann on CERT.org…
A look at a double-dipping advertising network
Online advertising is a multi-billion dollar industry that has evolved over time in how it reaches consumers. Generic pop-ups have largely…
Microsoft warns against new Internet Explorer Zero-Day UPDATED
Update (May 1, 2014): Microsoft has decided to release an out-of-band security update for CVE-2014-1776 and, in a surprising move, is also…
UPDATE: Apple in hot water after SSL/TLS validation fiasco
Update (Feb 25): More info on the update can be found here. Original story: Releasing a software update right before the…
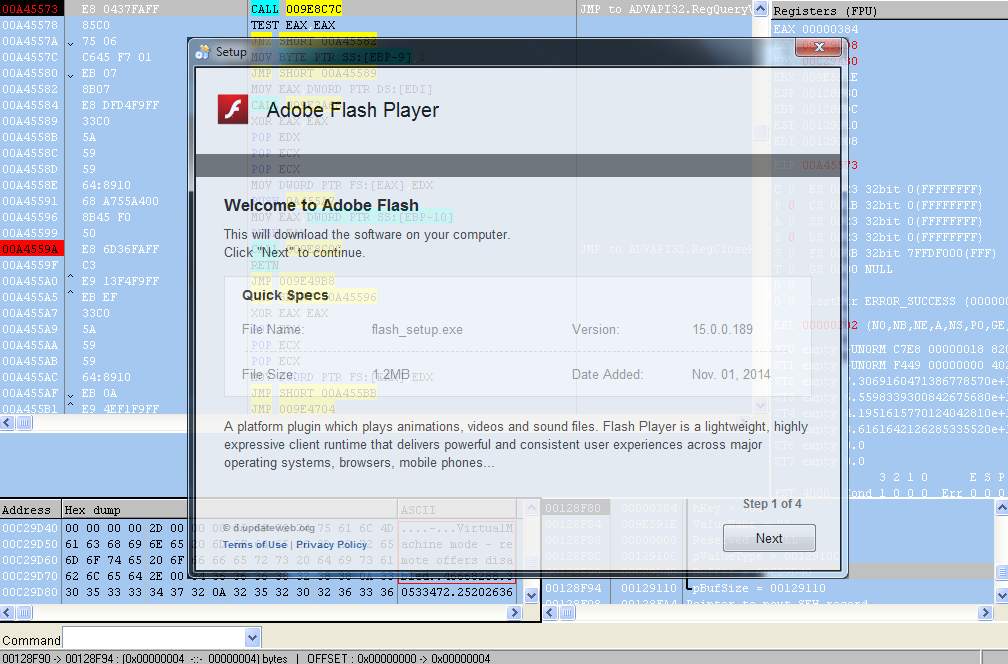
Adobe Flash Player Zero-Day: details and mitigation
Update (02/24/14): This exploit has been found in the wild already. It is blocked by Malwarebytes Anti-Exploit. In a very busy month…
Hiding in plain sight: a story about a sneaky banking Trojan
The Zeus/Zbot Trojan is one the most notorious banking Trojans ever created; it’s so popular it gave birth to many offshoots…
Tech support scams: Show me the money
Fake or rogue tech support companies are lurking everywhere. Whether they cold-call you or deceive you with ads and pop-ups, you…