Depending on the type and size of your organization, a DDoS (Distributed Denial of Service) attack can be anything from a…
Tag: protection
HTTPS… Everywhere!
We recently updated our redirections rule in HTTPS-Everywhere, a browser extension that automatically redirects you to the HTTPS version of the…
Torify and analyze traffic for your VM
Virtual machines are a great tool to run untrusted piece of software and analyzing the network activity. Most of the time,…
Yontoo: PUPs with two faces
Author’s Note: We at Malwarebytes continue to do our part in educating our product users and constant blog readers about day-to-day…
WebSearcher PUP applies Proxy Lockdown
What makes this one different? What makes this one different is that it uses a set of permissions to get the…
My Conversations with Cybersecurity Influencers
Today, we’re excited to be launching our thought leadership series entitled “Marcin’s Soundbytes.” You’ll see me interview some of the savviest…
Dell System Detect Vulnerability now classified as a PUP
UPDATE: After some updates of the latest versions of Dell System Detect, we have delisted this application from its previous classification…
10 tips to maintain an online presence in a privacy-hostile world
Online privacy is such a hot topic these days due in large part to the recent revelations about the NSA which…
Microsoft warns against new Internet Explorer Zero-Day UPDATED
Update (May 1, 2014): Microsoft has decided to release an out-of-band security update for CVE-2014-1776 and, in a surprising move, is also…
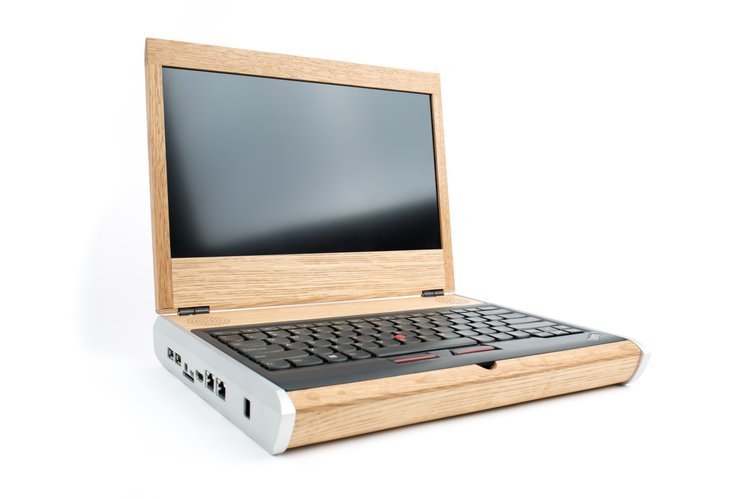
Open Source Laptop
A couple of months ago, I watched the live stream of the Chaos Computer Club with one of the talks called “The…