This month in ransomware: ALPHV and LockBit joining forces?
Tag: ransomware
Exposing the ransomware lie to “leave hospitals alone”
Ransomware gangs are getting more ruthless to increase the pressure on their victims. Now, even swatting cancer patients seems to be on the table.
Microsoft disables ms-appinstaller after malicious use
Microsoft decided to disable App Installer links by default after it noticed several access brokers using the handler to spread malware.
Oops! Black Basta ransomware flubs encryption
Researchers have found a flaw in the Black Basta ransomware encryption algorithm, allowing decryption of some files.
The top 4 ransomware gang failures of 2023
Ransomware gangs don’t always win, and when they don’t, it feels pretty great.
How ransomware operators try to stay under the radar
We look at the three most common methods that ransomware groups use to avoid being detected.
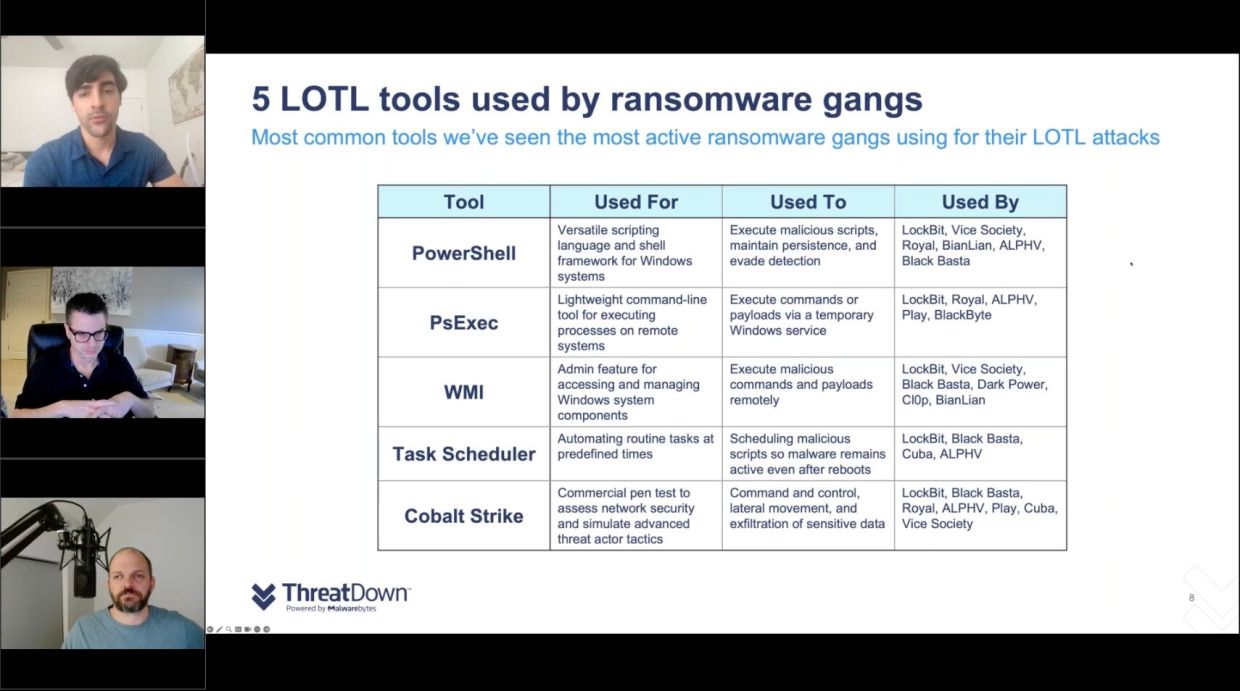
Webinar recap: Ransomware gangs and Living Off The Land attacks (LOTL)
Learn how RaaS gangs use LOTL tactics in their attacks on organizations.
Ransomware review: December 2023
In November, ransomware gangs attacked at least 457 victims—the highest monthly count in 2023, after May’s record numbers.
Healthcare giant Norton breach leads to theft of millions of patient records
Ransomware operator ALPHV/Blackcat reportedly stole 2.5 million records from non-profit healthcare system Norton Healthcare
Ransomware review: November 2023
In October, we witnessed the takedown of several high-profile groups, including alleged Sony attacker RansomedVC.