The password management company LastPasss notified customers in late December about a recent security incident. The notice was posted as an update of…
Tag: security
Epic Games introduces safer accounts for kids
Epic have made some alterations to how accounts for kids work, with multiple features disabled for what are now known as…
Hive Social pulls the plug on itself after security flaws found
You may well have changed your social media site of choice recently, but that doesn’t mean the security implications of less…
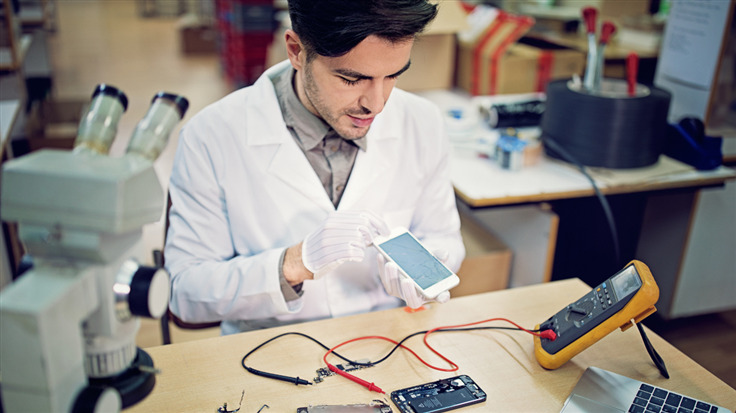
Maintenance Mode aims to keep phone data private during repairs
One of the biggest data related headaches you’ll face with a mobile device is what do to in the event of…
Security awareness campaign highlights things your bank will never say
If you like anti-phishing efforts, hashtags, and confusing but colourful video games, you’ll be interested to know that a security initiative…
Welcome to high tech hacking in 2022: Annoying users until they say “yes”
Last week we learned that ride-sharing giant Uber’s defences had been unpicked by an attacker with a novel take on social…
Wrestling star Mick Foley’s Twitter compromised, selling PS5 consoles
One of the biggest wrestling stars around, Mick Foley, had his Twitter account hijacked in an attempt to legitimize a very…
Tor’s (security) role in the future of the Internet, with Alec Muffett
Tor has a storied reputation in the world of online privacy. The open-source project lets people browse the Internet more anonymously…
Tips to protect your data, security, and privacy from a hands-on expert
This post was authored by one of the most active helpers on the Malwarebytes forums who wishes to remain anonymous. Back…
Let’s Encrypt to revoke “mis-issued” certificates
If you use a Let’s Encrypt SSL/TLS certificate, you may wish to check your account over the coming days. Revocation is…