Hello, we are calling from Windows and your computer looks like it is infected. Our Microsoft Certified Technician can fix it for you.
Sound familiar? Whether you have just been scammed or simply want to find out more on the topic, you have come to the right place.
Tech support scams are a million-dollar industry and have been around since 2008. Every single day, innocent people are tricked into spending hundreds of dollars on non-existent computer problems.
There is no sign of these scams slowing down, despite several actions taken by the Federal Trade Commission.
Perhaps even worse, companies right here in North America are now pulling the same tricks and taking advantage of existing and prospective customers replying to online ads.
The purpose of this page is to gather all the information we have collected over time into one place that you can use as a go-to resource when you need it.
Sections
How tech support scams work
Tricks you should look out for
Getting help if you have been scammed
Reporting the scam
Related articles
How tech support scams work
Cold calls from fake Microsoft (etc.) agents
The scam is straightforward: pretend to be calling from Microsoft, gain remote control of the machine, trick the victim with fake error reports and collect the money.
If you ever get a call from a Microsoft or Windows tech support agent out of the blue, the best thing to do is simply hang up. Scammers like to use VoIP technology so their actual number and location are hidden. Their calls are almost free which is why they can do this 24/7.
As per Microsoft:
“You will never receive a legitimate call from Microsoft or our partners to charge you for computer fixes.“
Toll-Free Numbers (TFN) for fraudulent tech support companies
Located in India but also in the US, these companies heavily advertise on popular search engines as well as websites with high traffic. People call them for assistance and get fooled with similar techniques employed by Indian cold callers.
Another source for these companies comes from some of their existing customers or customers of parent companies sent to them. The remote technician upsells the customer who only came to activate their software but ends up forking hundreds of dollars on “Windows support.”
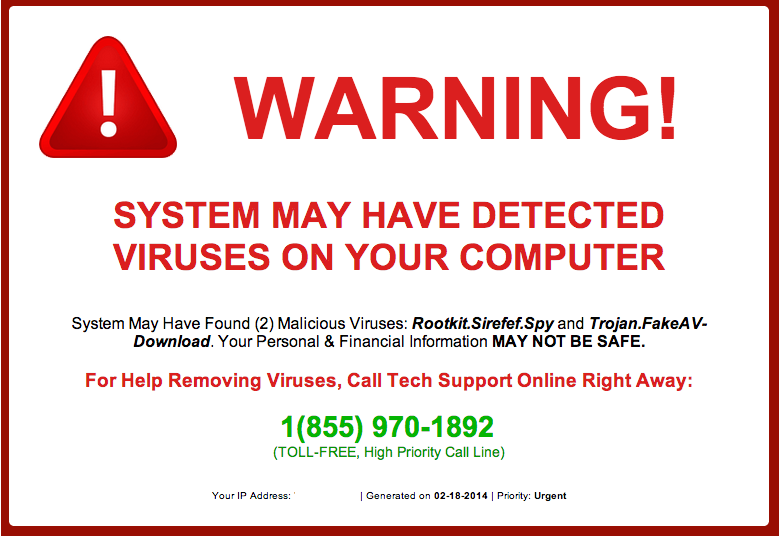
Fake pop-ups claiming your computer is infected—reminiscent of FakeAV—are used by scammers to reel in innocent victims.
If you decide to call in for remote computer assistance, you need to be very careful about which company you are going to deal with. Simply picking the top ad on a search results page could end very badly.
Unfortunately, the company or technician being from the US is not a guarantee for honest service. Many businesses in the US are using dirty tricks to take advantage of people, with the unsavvy and elderly as their prime targets.
If you don’t feel comfortable doing this online, brick and mortar computer repair shops are a good alternative.
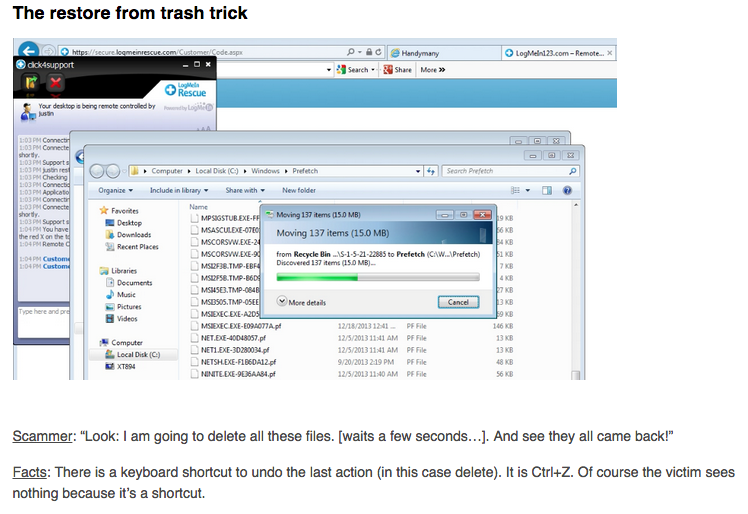
Remote access
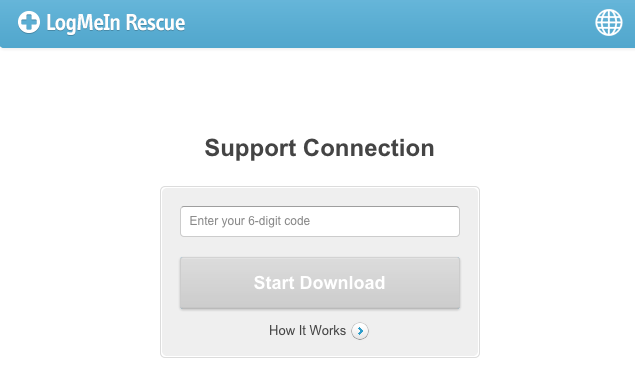
The ‘technician’ requests to have remote access to your computer and may use remote login software to do so. Note that while these applications are perfectly legitimate, it is important to remember that
if you run this type of software, you are effectively giving a complete stranger total control of your computer.
Screenlockers
A method that has been gaining popularity by tech support scammers is to spread malware with the sole purpose of locking the user out of his own computer. We call this type of malware screenlockers and the installers are detected as Rogue.TechSupportScam. They may look like a BSOD (Blue Screen of Death) or a warning that you are using illegal software (asking for a registration key). The malware is offered as part of a bundle or posing as an installer for something else.
The ones that look like a BSOD usually have a telephone number on them that belongs to the scammers outfit. Once you call that number they will tell you a trick to get rid of the BSOD to gain your trust, but of course the trick was built into the program for that reason.
The type asking for a registration number usually has a telephone number as well, but often they come with a few links that will open sites with popular remote assistance/desktop software like TeamViewer, LogMeIn, Ammy Admin, Supremo, and others. In these cases, the scammers will ask you to install that software and give them your access code, so they can “repair” your computer. Selling you overpriced solutions and “service contracts” is the real goal, obviously.
If you are interested in some examples, we have blog posts on the following:
- Tech support scammers using Winlogon
- Tech support scammers get serious with screen lockers
- Tech support scams and the Blue Screen of Death
- Dodge four tries to escape from being scammed
Should you be confronted with one of these screenlockers, do a search on our forums for the displayed telephone number. With any luck, we have already reverse engineered the screenlocker, and you can find a removal guide among the Malware Removal Self-Help Guides for your particular version.
Tricks you should look out for
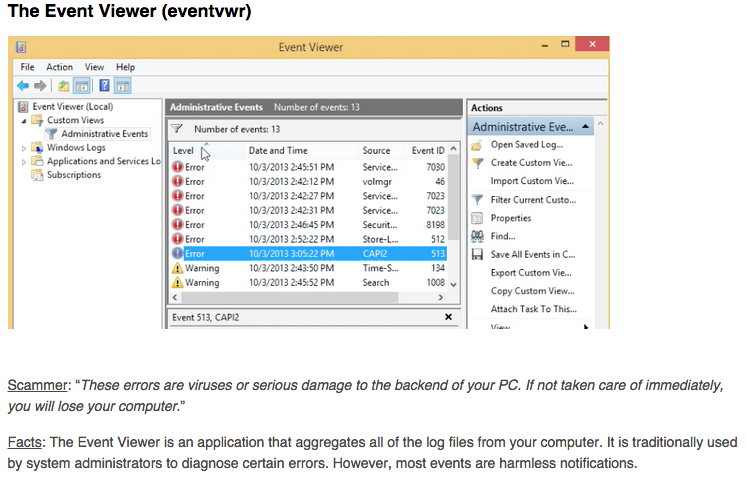
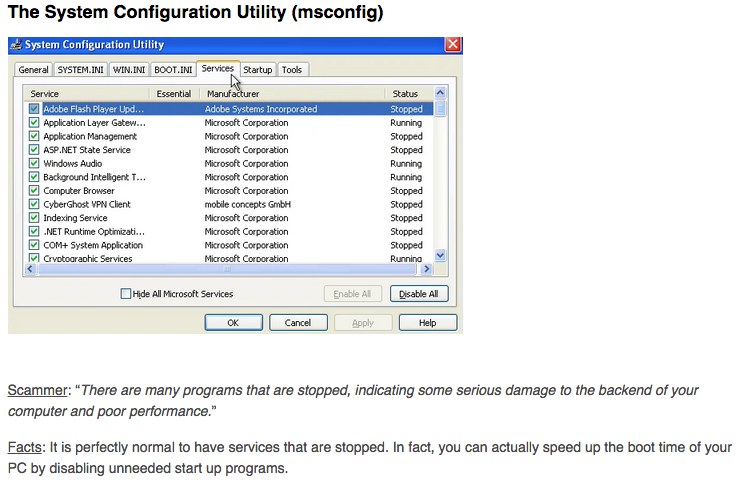
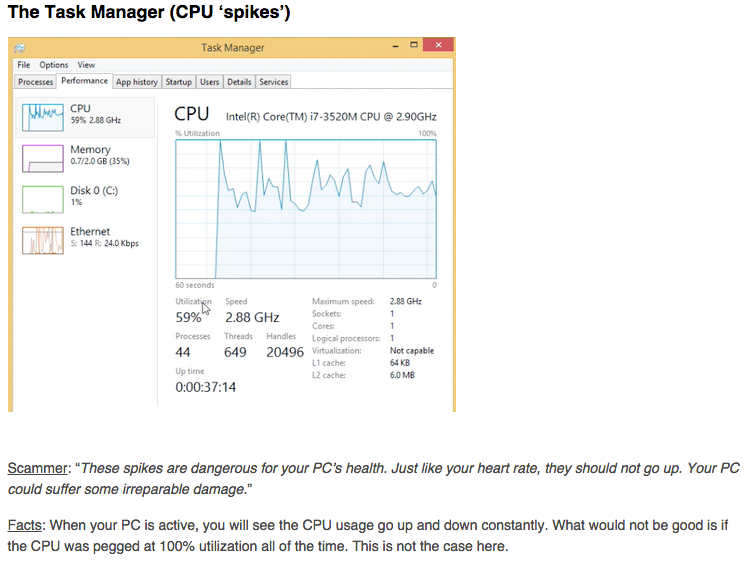
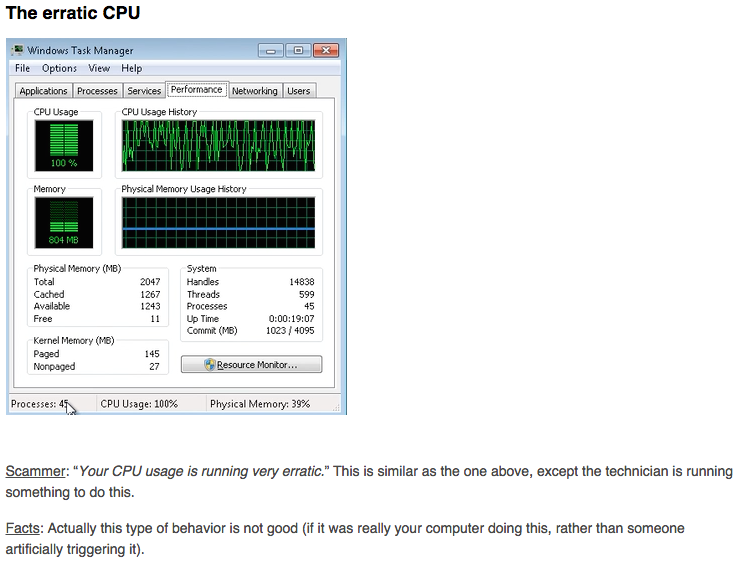
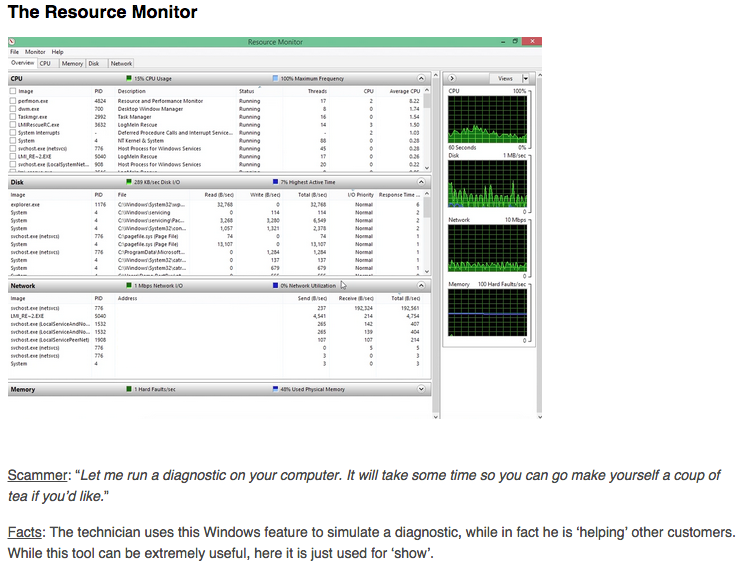
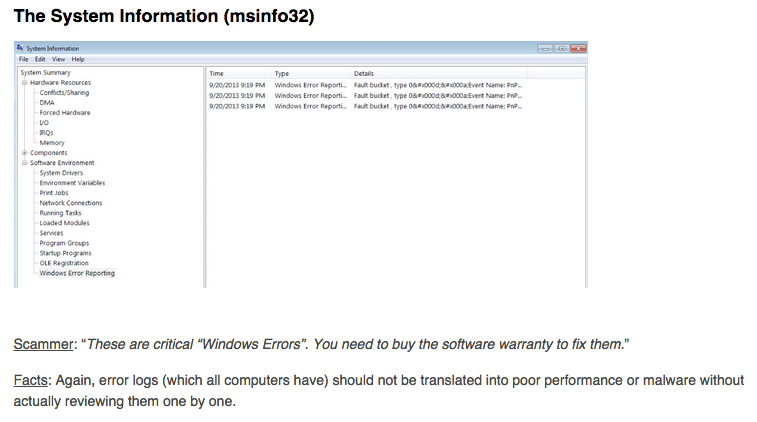
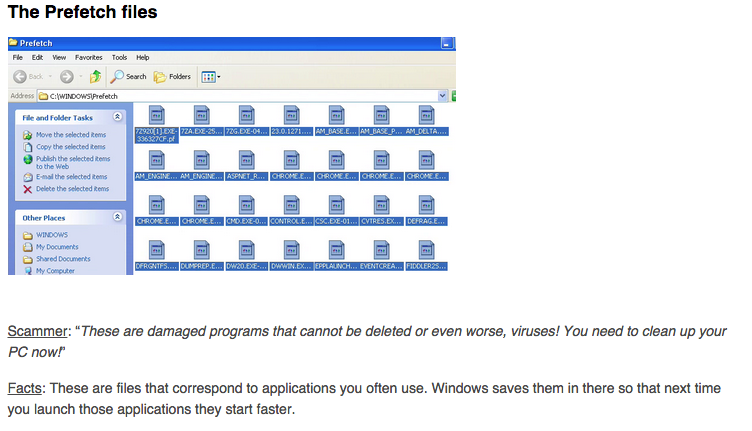
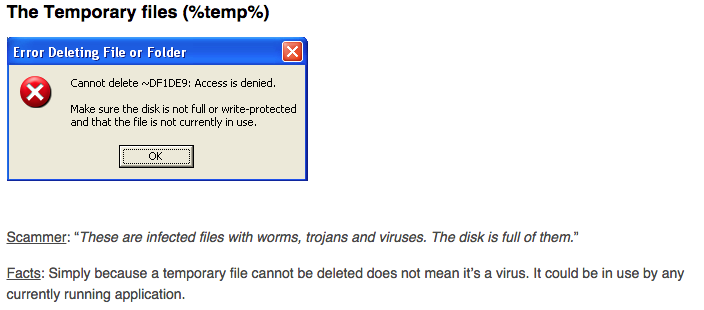
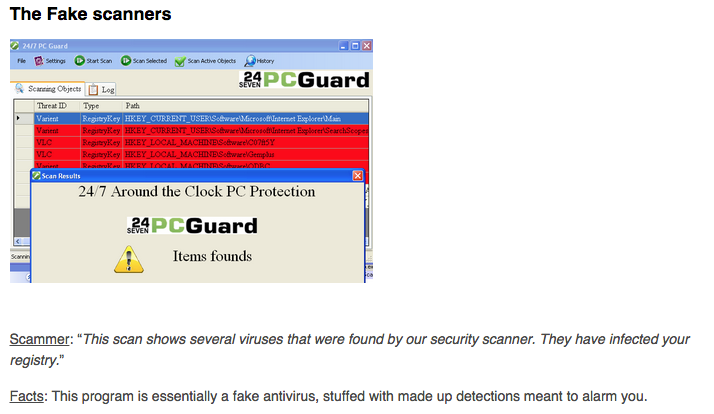
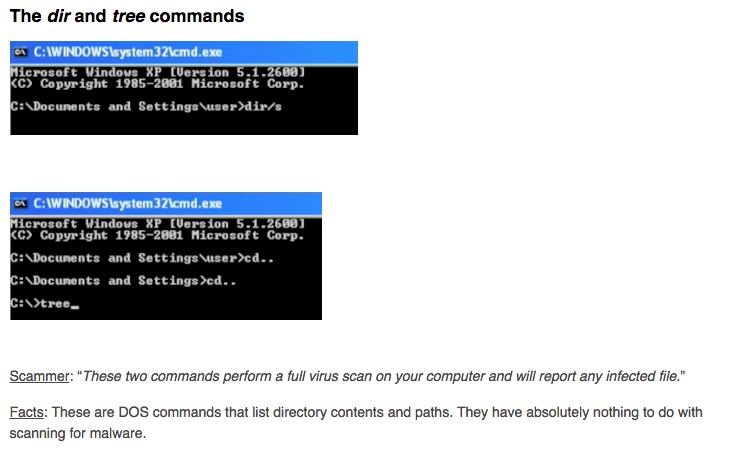
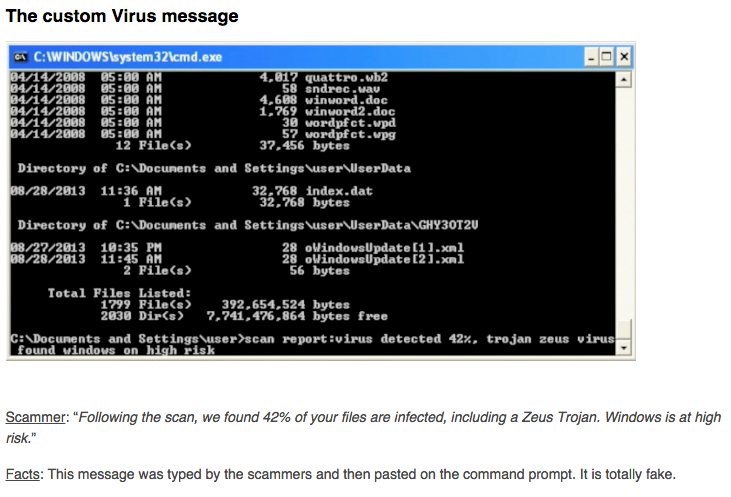
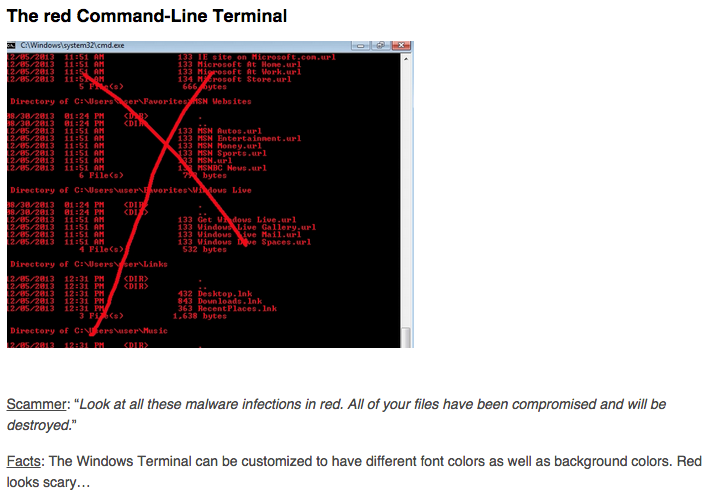
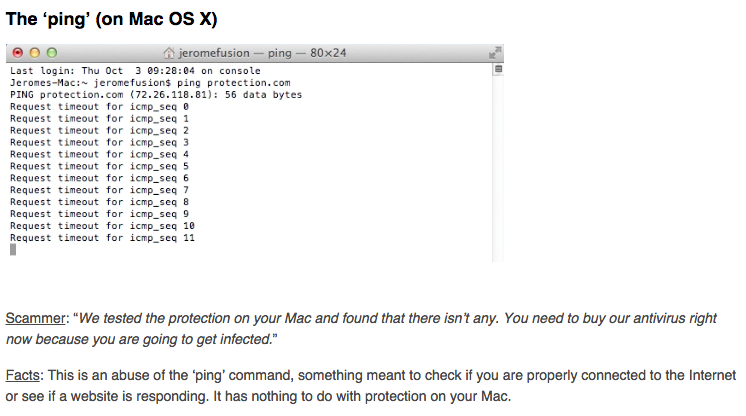
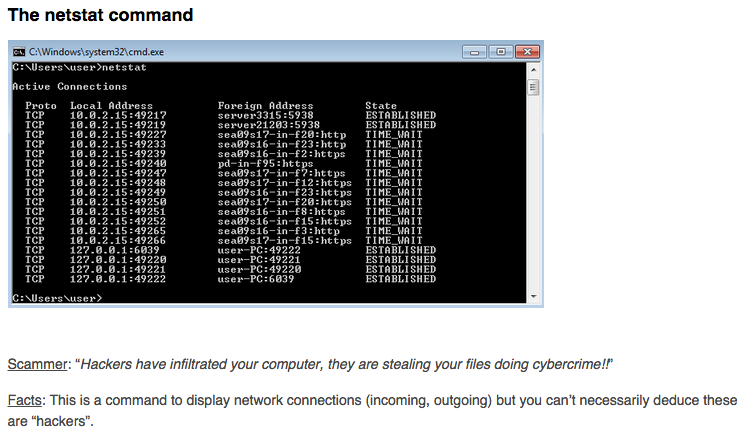
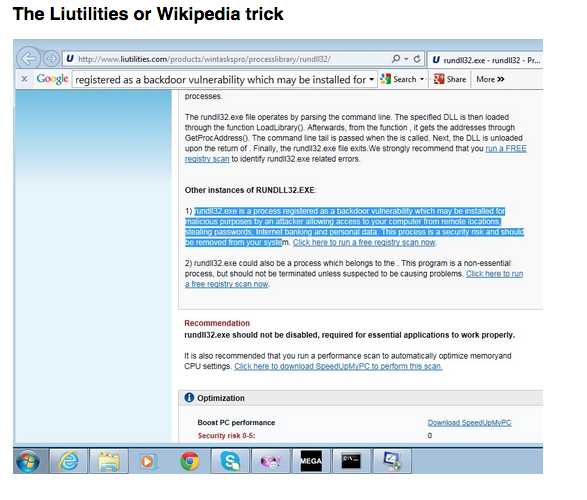
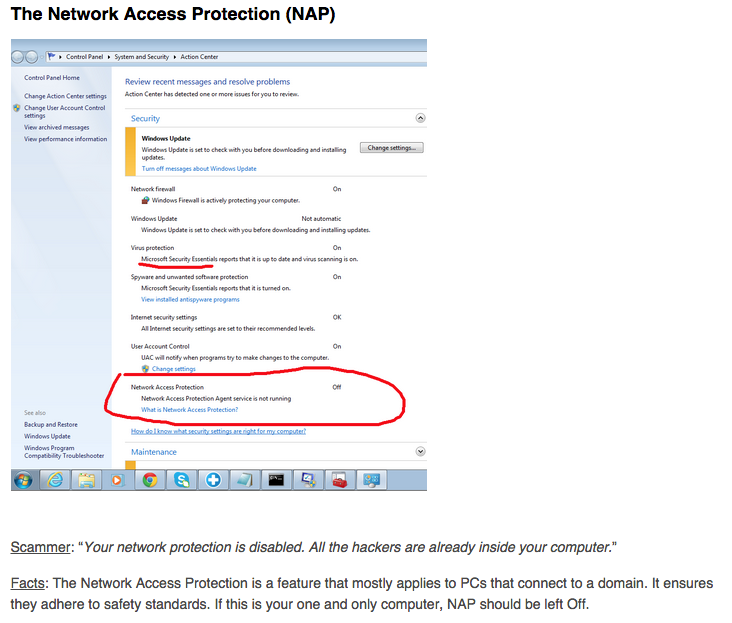
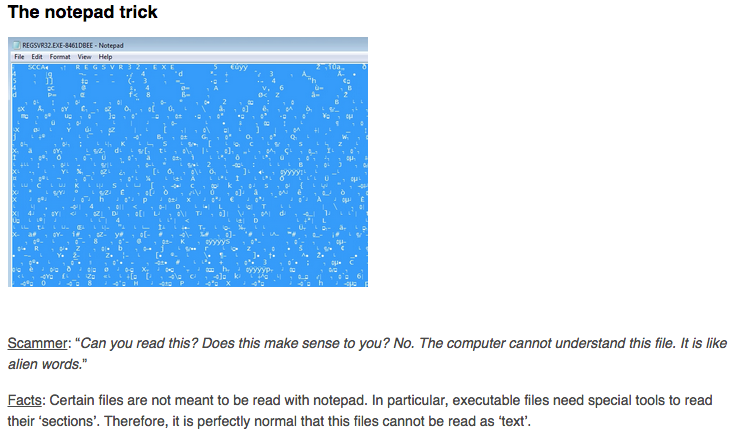
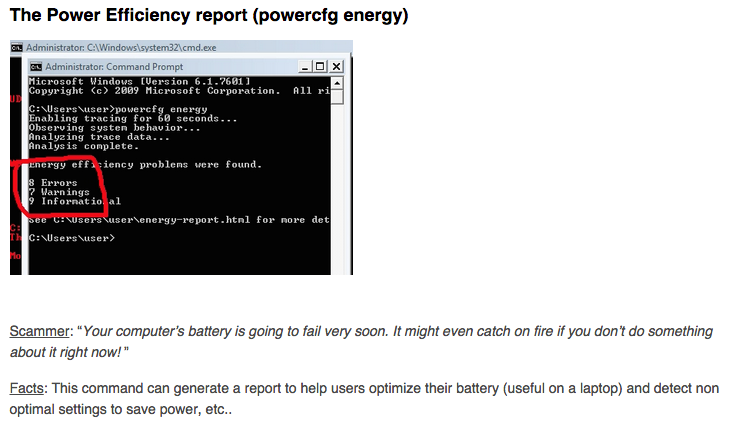
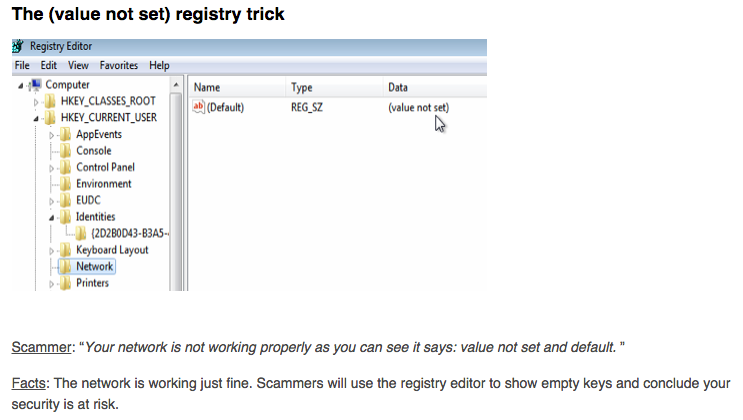
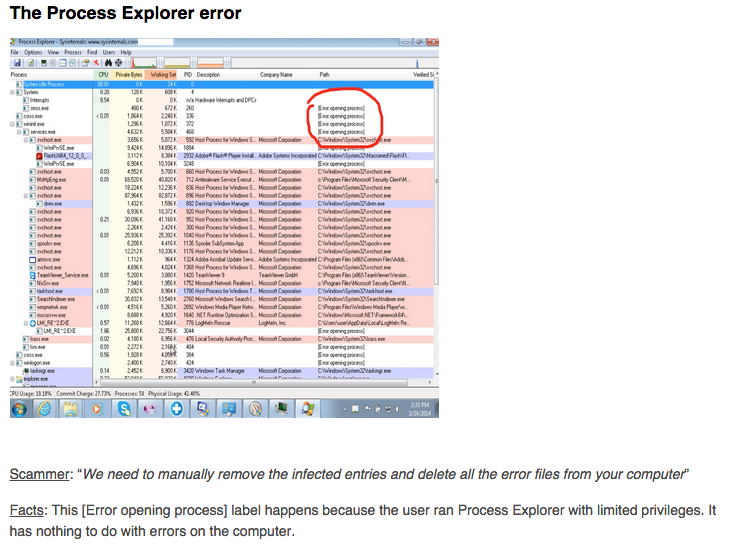
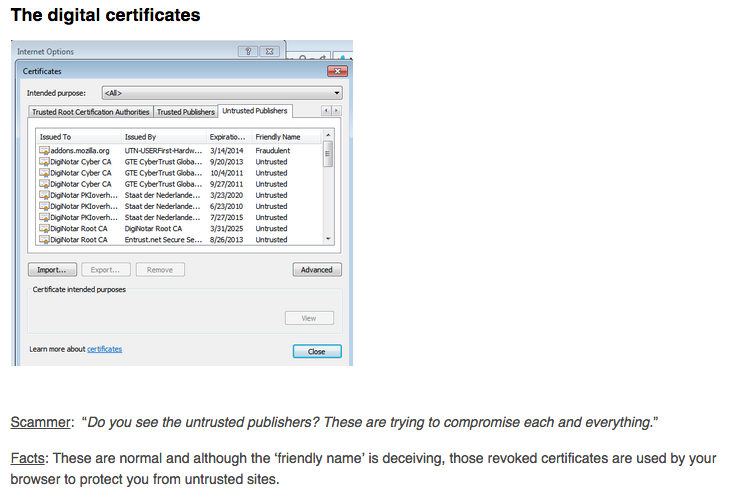
Once logged into your computer, the remote technician will attempt to trick you by fabricating errors or even viruses on your computer. They like to use the default Windows tools and turn them against you, hoping you’ll get scared and follow up their directions.
Getting help if you have been scammed
Getting scammed is one of the worst feelings to experience. In many ways, you feel like you have been violated and are angry to have let your guard down. Perhaps you are even shocked and scared, and don’t really know what to do now. The following tips will hopefully provide you with some guidance.
If you already let them in
- Revoke remote access (if unsure, restart your computer). That should cut the remote session and kick them out of your PC.
- Scan your computer for malware. The miscreants may have installed password stealers or other Trojans to capture your keystrokes. Use a program such as Malwarebytes to quickly identify and remove threats.
- Change all your passwords. (Windows password, email, banking, etc.)
In some cases (i.e., you did not pay or called them names), scammers will seek revenge on your machine. Here are some things they might try and what to do to recover from them:
- Master password lock out
There are various “hacks” to reset that password. One method is to use a Linux boot CD to mount Windows and then use the chntpw utility. It is described in this Ask Ubuntu page.
- Missing software drivers
First, try to do a System Restore. If it fails, you should be able to reinstall them by going to the manufacturer’s website and downloading the appropriate driver.
- Missing files
First, try to do a System Restore. If it is not available, check for backups you may have made and stored somewhere else. As a last resort, there are programs that can scrape your hard drive and attempt to recover the missing files.
If you already paid
- Contact your financial institution/credit card company to reverse the charges and keep an eye out for future unwanted charges.
- If you gave them personal information such as date of birth, Social Security Number, full address, name, and maiden name, you may want to consult the FTC’s website and report identity theft.
Reporting the scam
File a report
- In the US: File a complaint (FTC) | More information about online fraud | Florida Attorney General
- In Canada: Contact law enforcement
- In the UK: Report fraud | Report cold call
- In Australia: Report a scam
Shut down their remote software account
- Write down the TeamViewer ID (9-digit code) and send it to TeamViewer’s support. They can later use the information you provide to block people/companies.
- LogMeIn: Report abuse
Spread the word
You can raise awareness by letting your friends, family, and other acquaintances know what happened to you. Although sharing your experience of falling victim to these scams may be embarrassing, educating the public will help someone caught in a similar situation and deter further scam attempts.
Investigate
While hanging up is the safest thing to do when you get a cold call, some people have gone on a mission to expose those scammers. While we don’t endorse this behavior, if you do have information to share, please let us know and we will update this page with any new relevant details.
Related articles
- Phone scammers call the wrong guy, get mad and trash PC
- Tech support scams: a look behind the curtain
- Online PC Support Scams: Turning the Tables
- Tech Support Scams: Coming to a Mac near you
- Tech support scammers spam YouTube with robot-like warnings
- Tech support scammers target smartphone and tablet users
- Tech support scams: Show me the money
- Netflix Phishing Scam leads to Fake Microsoft Tech Support
- The Tax Season Tech Support Scam
- Netflix-themed tech support scam comes back with more copycats
- Beware of US-based Tech Support Scams
- Tech Support scammers rip big brand security software with fake warnings
- Tech Support Scams exposed at VB2014
- Tech Support website infects your computer before you even dial in
- PSA: Tech Support Scams Pop-Ups on the Rise
- Mac users: Beware of increased tech support scam pop-ups
- A New Twist on Tech Support Scams Pop Ups
- Tech Support Scammers Go For Pornographic Shocker
- TechSupportScams And The Blue Screen of Death
- Defeating The Fake iOS Crash Reports
- The Multi-language Tech Support Scam is Here
- Malvertising Via Google AdWords Leads to Fake BSOD
- Beware of Tech Support Impersonators
- Tech Support Scam Asks for Passkey
- Tech Support Scammers Impersonate Apple Technicians
- Comcast Customers Targeted In Elaborate Malvertising Attack
- Tech Support Scammers Lure Users With Fake Norton Warnings, Turn Out To Be Symantec Reseller
- Tech Support Scammers Use Subdomain Trick To Defeat Blocking
- Scammers Impersonate ISPs in New Tech Support Campaign
- Tech Support Scammers Bring Back FakeAV
- The hunt for tech support scammers
- Tech support scammers get serious with screen lockers
- Tech support scams and Google Chrome tricks
- Tech support scam page triggers denial-of-service attack on Macs
- Rogue Chrome extension pushes tech support scam
- The numeric tech support scam campaign