As much as we want to imagine the cybercrime underground as a dark alley full of sneaky types dressed in ski masks and gloves, the reality is that in many cases, it’s comprised of highly organized business units.

Business units of fedora wearing masked men
These units not only create, buy and distribute malware but also look for new infection opportunities in pre-existing user bases, say for example those that use browser extensions.
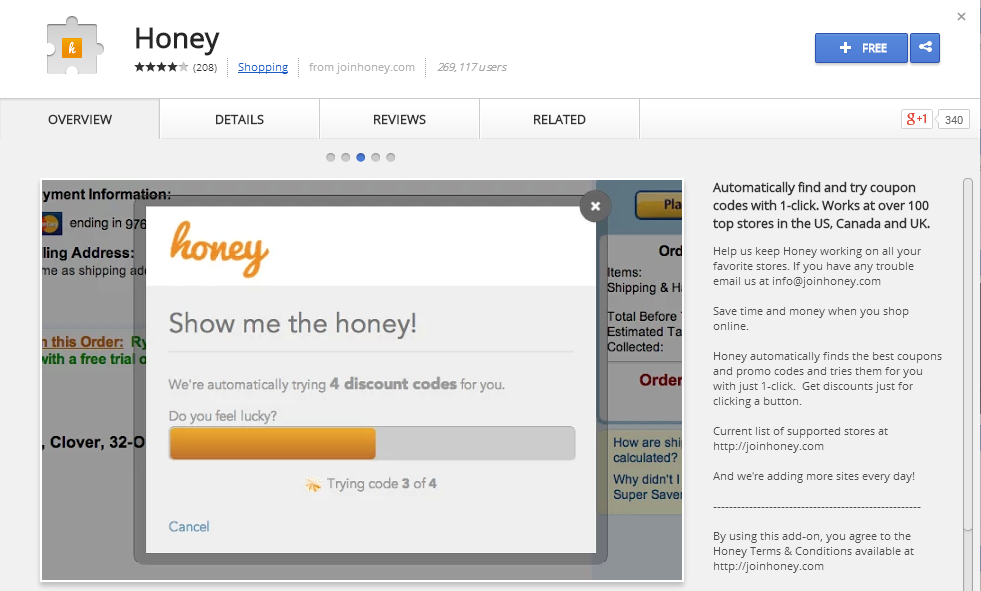
In a recent “Ask Me Anything” (AMA) on Reddit, the developer of a popular coupon-finding Chrome extension called Honey talked about cybercrime units offering to buy out his company.
They even offered the company a six-figure sum, per month, for use of the product.
Luckily, the guys at Honey are admirable to the core and refused any kind of selling or cooperation with the group before a number was even mentioned.
The same, however, did not apply to one developer who sold his easily developed product for a four-figure sum and found it a month later being used to push malware and other such badness.
It was about a month ago that I wrote about bug bounties and whether or not they had a place in the computer security world. Today, I think this discussion about selling out to the wrong folks is just as important.
With bug bounties, the benefit is that by buying vulnerabilities from researchers who might otherwise sell them to cyber criminals, the products are safer for users.
At the same time, by not selling a product to cyber criminals, regardless of how much they claim to be able to pay, developers of all applications are taking a stand and providing an example to the rest of the technology world:
“We create things to make the world a better place.”
Thanks for reading, safe surfing and DFTBA!











