Since December of 2011, the spread of malicious advertisements, or “Malvertisements”, has drastically increased. Along with this trend is the increased spread of some pretty nasty malware. One in particular is called Happili, an adware trojan that installs a browser extension to re-direct legitimate search queries to ad sites.
Double Vision
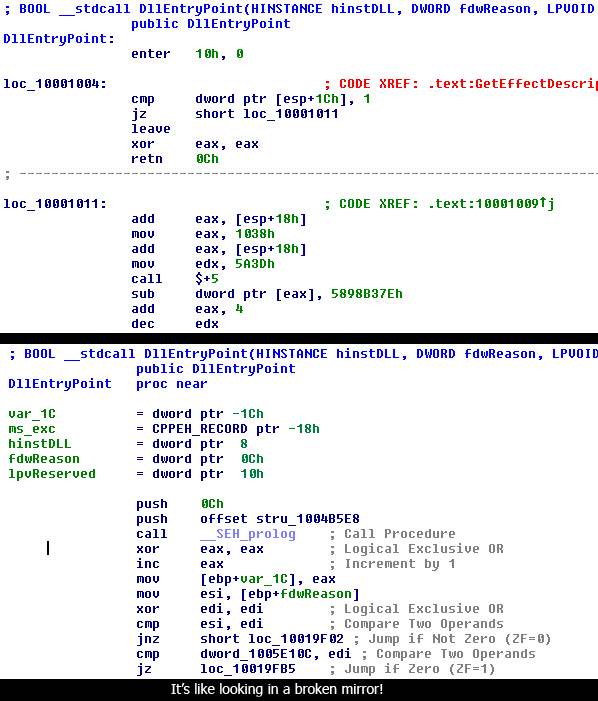
Happili has been especially difficult for many of the major Anti-Virus companies because of how closely the malware resembles legitimate files. This method of obfuscation makes it so that if the anti-virus companies attempt to use signature based detection using the normal criteria, they will end up with a lot of false positives because legitimate files will be flagged as malicious. This could cause a lot of problems for the end user as well as the company itself and therefore normal signatures cannot be used. Instead, most companies look for nuances in the files themselves to detect whether it is truly Happili or not. This can take from a few days to a few weeks, however, and in the meantime Happili can run rampant without any detection. Happili is very unique, it is apparent that the creators of Happili have put a lot of effort into their design and attempts at hiding the malware files. Here are some examples:
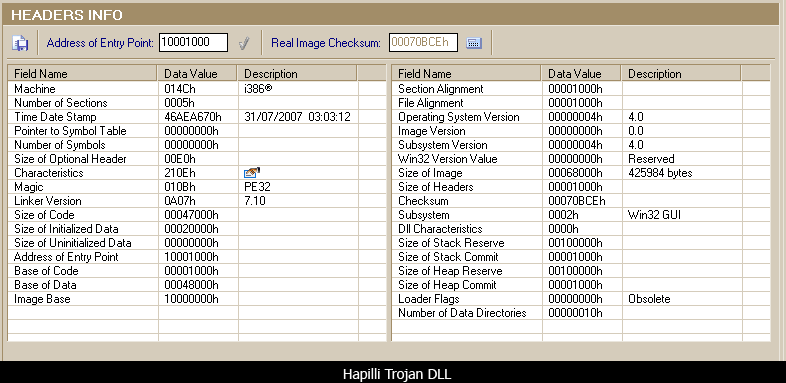
The above image is a screenshot of the Happili Trojan DLL’s header information, taken from PE Explorer.
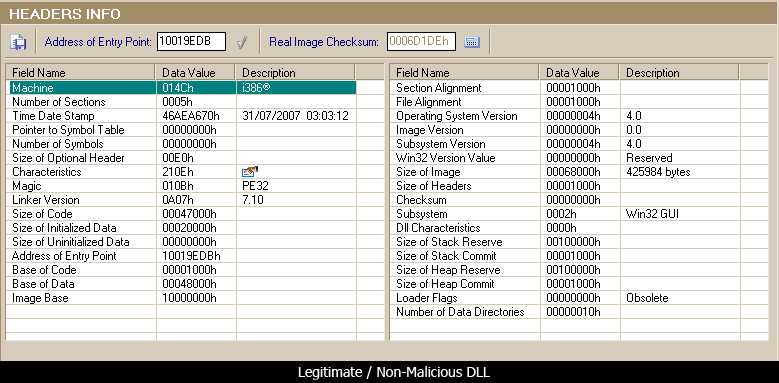
This is the same view of the non-malicious DLL which Happili is attempting to impersonate.
If you notice, nearly every single header value between the two files is identical, all that is except for the Address of Entry Point. If we look at the section headers, we see the same thing:
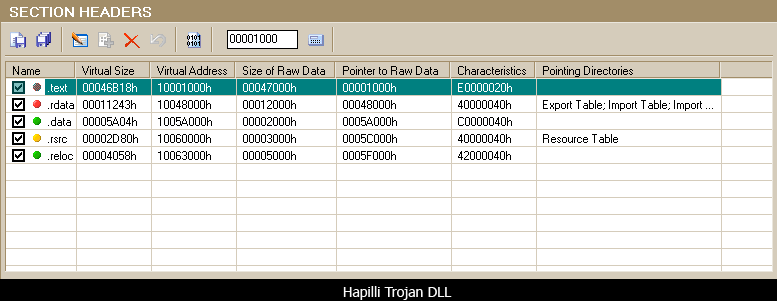
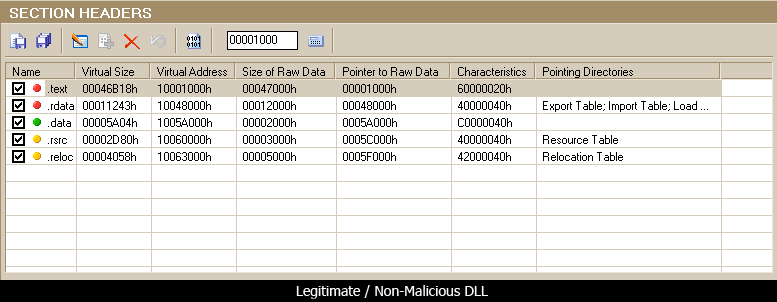
The only difference is in the .text section, which has different characteristics from the legitimate DLL.
See – the most effective way of using heuristic definitions for malware detection is:
- Take one sample, check for unique attributes about that file that are deeper than what you would see on the surface
- Write a definition that checks for these unique values.
- Usually this results in being able to find variants or different iterations/versions of the same malware.
Happili can overcome this method of detection because of how well it is disguised as a legitimate file. This means that detecting differences from the surfaces could be difficult, although once the underlying code is exposed it’s obvious which file is legitimate and which is not.
Execution
Happili’s dropper executable performs multiple operations with the end goal of complete infection the default web browser and system persistence establishment. It will accomplish this by:
- Dropping multiple files in multiple locations
- Creating registry keys and setting values to establish persistence of the malware (executing the malware every time the operating system starts)
- Executing the malicious DLL’s by running them with the Windows library execution application “RunDLL32.exe”
- Infecting the web browser with either an injected DLL or installing an extension which will redirect the users during searches.
The redirects will not happen every time and with every search. Once the user navigates to a search engine, enters their search query and clicks on one of the results, the malware will randomly redirect the user to one of many different sites depending on the search value. Here is an example of me performing a search for the term “Ipad” in Google while using an infected version of Chrome:
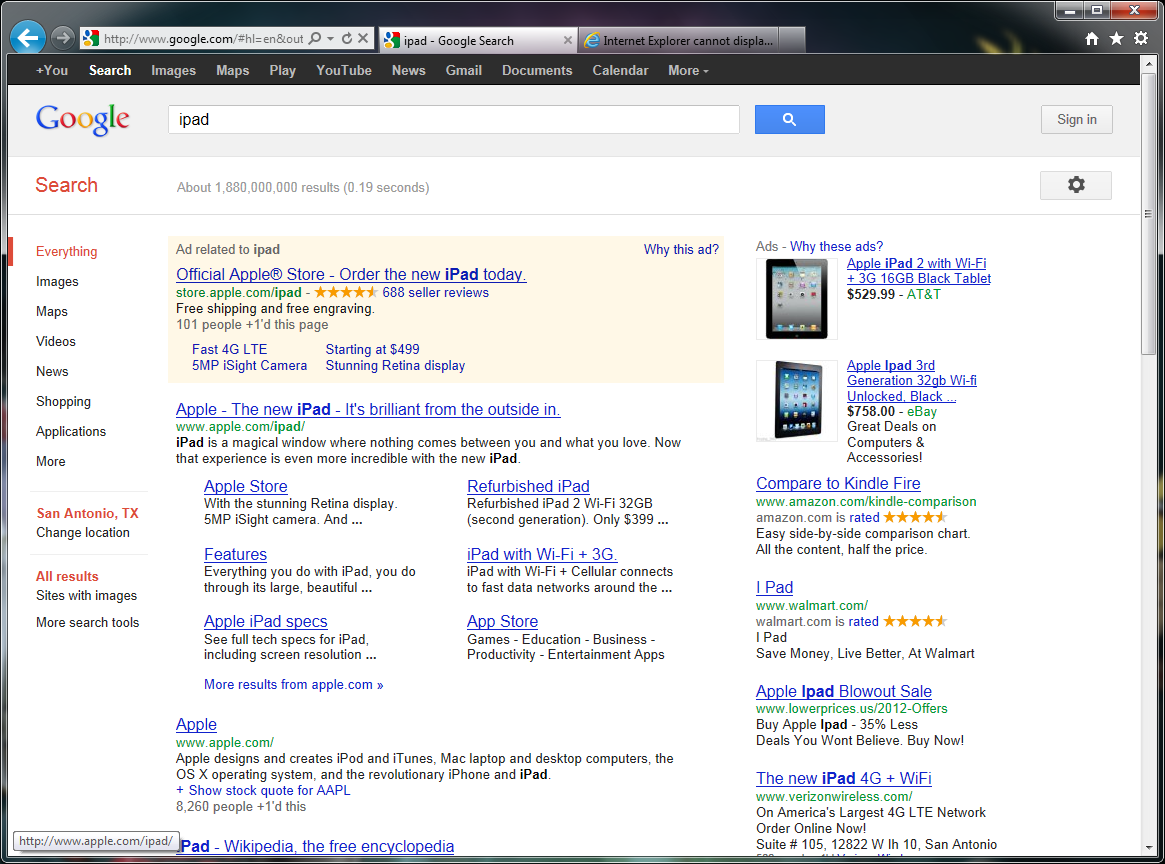
So far so good, so I click on one of the first links and before I know it…
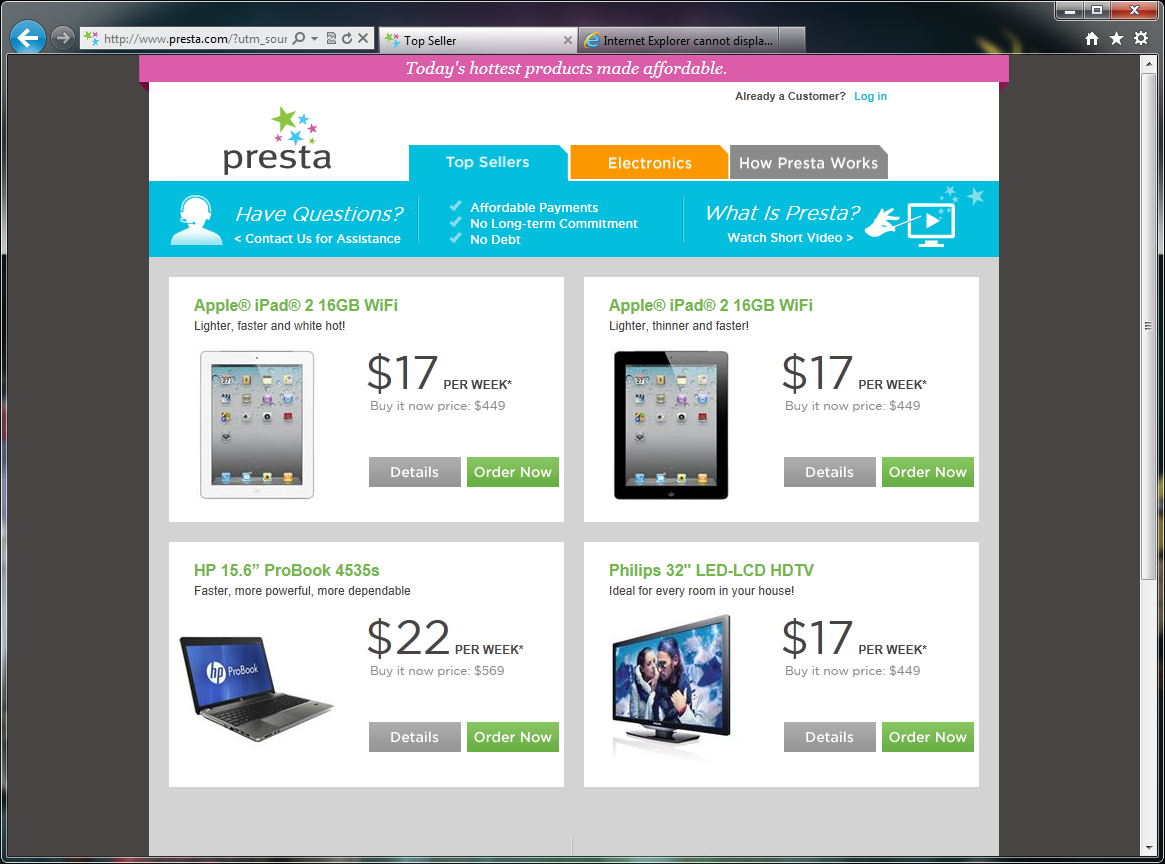
This doesn’t look like “apple.com”. So I go decide to open Firefox and try a search for Android Phones…
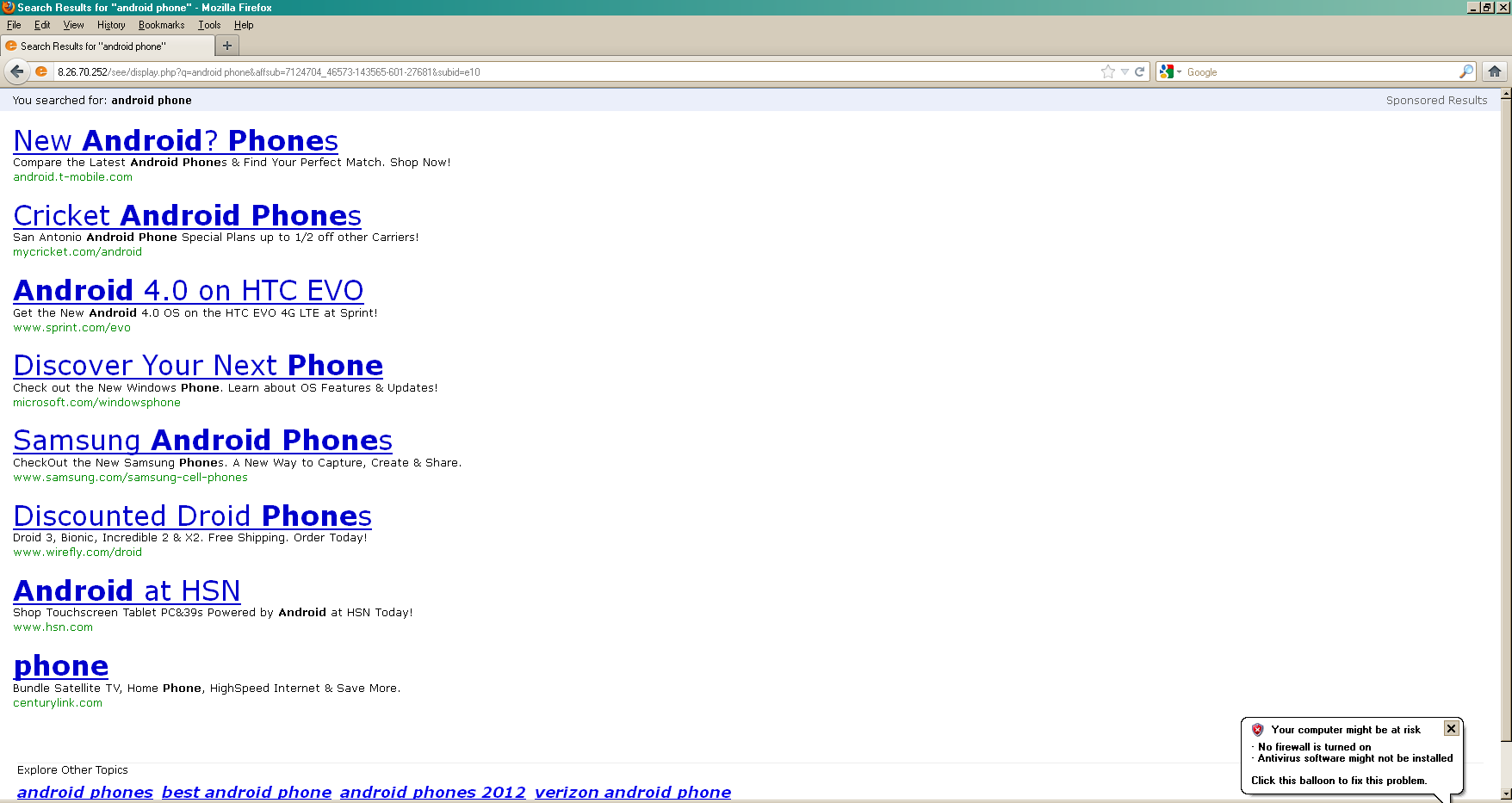
After some more research and testing, I found that you are more likely to get redirected depending on the search term and the browser. For example, Internet Explorer gets redirected the most while Firefox and Chrome redirects are farther in between. Popular terms are more likely to redirect you sooner, like the ones I used above. With random search terms you usually get something like the search screen above. For merchandise you might get redirected to a shop site or an auction site, these are most likely fake or malicious in some way so I would recommend not entertaining the idea of using them to buy things. For adult terms, you get redirected to whatever porn site the malware decides to send you to.
As I said before, Firefox and Chrome are infected by the malware when it installs extensions into the browser; here is what these extensions look like:
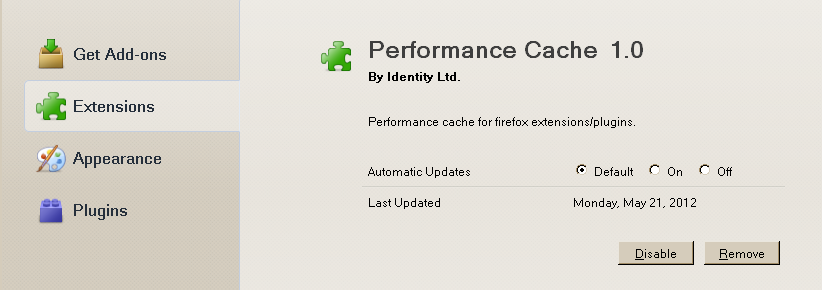
These extensions are what allow the malware to redirect your web searches and therefore are bad! Combined with the fact that they are incredibly vague and mildly “legitimate” looking, a normal user might not think twice that these extensions are in fact the cause of their misery.
Infection
There has been a drastic increase in the amount of malicious advertising going on since December of last year. These ads do everything from redirect users to Fake AV sites, to downloading and executing malware by exploiting the browser or its plugins. These types of ads are put into the system by gangs of cyber criminals who either want to spread spam or steal personal information.
The Happili Trojan is one of the many types of malware being distributed by these ads and could be downloaded and executed without you ever even knowing what had happened. There is also something to be said for the purpose of Happili (spreading spam/redirecting) and the method in which it is set to attack a victim system. This kind of Malvertising trend is not going to go away any time soon, since modern day cyber-crime revolves around making money and what better way to do that than advertising.
Protection
The best way to remove a Happili infection is to never BE infected with Happili in the first place. As stated before, one of the most currently common methods of infection is by malicous advertisement drive-by attacks. “Malvertisements” could be on any site you visit at any time so you should always give yourself a fighting chance by following these guidelines:
- Always keep your browser up to date with the latest security patches
- Always keep your plugins up to date with the latest security patches
- Always keep your operating system up to date with the latest security patches
- Don’t click on anything you don’t trust or a link sent to you from someone you don’t trust.
- Use a sandboxed browser
The first four sounded like something anybody should do and can do but that last one was probably a little confusing, let me explain further.
Sandboxie
The application Sandboxie is a free and open source sandbox. This allows the user to execute any process or application and prevent any modifications being made to the base operating system. Sandboxie is great if you want to surf the web without fear of being infected by “malvertisements” because it works perfectly well with your web browser. Here is an example of what would happen if you didn’t use a sandbox browser:
- You navigated to one of your favorite web sites
- At that exact moment, a malicious ad suddenly appears on the web page you are viewing
- The malicious ad exploits one of the various plugins you have installed with your browser and executes malware
- The malware infects your system and redirects you to pictures of celebrities with mustaches….forever.
- You are inspired, so you grow a mustache but no-one likes it (especially if you are a girl)
- All your friends and family abandon you and you live the rest of your life in misery and loneliness.
Now what would happen if you used the Sandboxie browser?
- You navigated to one of your favorite web sites
- At that exact moment, a malicious ad suddenly appears on the web page you are viewing
- The malicious Ad exploits one of the various plugins you have installed with your browser and drops and executes malware
- You close the Sandboxie browser
- Your system is fine and nothing else happens.
- You buy a winning lottery ticket with the money you might have spent on mustache crème.
- You live the rest of your life happy and rich.
I think my point is made. Navigate over to http://www.sandboxie.com/ and download Sandboxie! It’s super easy to download and install and if you need help, the Sandboxie website has a great FAQ section. There are also numerous YouTube videos on how to install, operate and profit from Sandboxie.
Removal
OK, so the section on protection wasn’t that helpful to you you’re infected and you need not to be. Here is how:
- Download and install Malwarebytes Anti-Malware
- If you have already done that, update the definitions to the most current ones
- This is an important step because the researchers and analysts here at Malwarebytes work 24/7 – 365 on developing new definitions to detect malware.
- We are also currently detecting all new variants of Happili, even ones which have a 0% detection rate on VirusTotal.
- Scan your system
- Remove all the infections
- Resume your life.
If you have Firefox or Chrome installed, most likely you will still have the extensions listed in your browser, however the files which made those extensions work are now gone so they shouldn’t cause you any more problems. For safe measure, see if you can find them and remove them manually; reference the section on ‘Execution’ to get a good idea at what the extensions might look like. If you see a suspicious extension, do a search for its name and make sure it’s not something important to you before you remove it. Happy Surfing!












