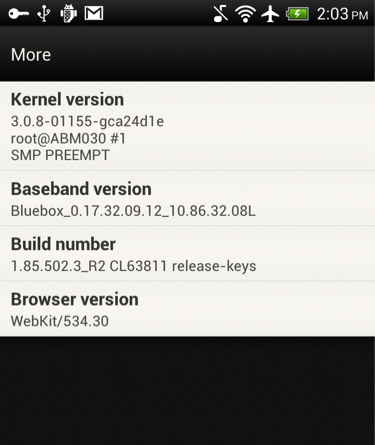
Yesterday, Bluebox Security unveiled in a corporate blog post that their research team—dubbed Bluebox Labs—had uncovered a vulnerability that affects 99% of Android devices. The vulnerability has been reported as existing since Android 1.6 (“Donut”) and may be plaguing some 900 million devices.
According to the firm’s CTO Jeff Forristal, the vulnerability allows a hacker to “modify APK code without breaking an application’s cryptographic signature, to turn any legitimate application into a malicious Trojan, completely unnoticed by the app [Google Play] store, the phone, or the end user.”
The blog also states the vulnerability gets even scarier when you consider altering applications created by the manufacturer (Samsung, HTC, etc), which inherently run at a higher privilege level.
“Installation of a Trojan application from the device manufacturer can grant the application full access to Android system and all applications,” says Forristal. “The application then not only has the ability to read arbitrary application data on the device (email, SMS messages, documents, etc.), retrieve all stored account & service passwords, it can essentially take over the normal functioning of the phone and control any function thereof.”
However, even if an update were produced by manufacturers, most Android users receive updates through their carriers, which don’t have the best track record for pushing updates to users.
To provide a figure of how behind some Android users are, some 36% of devices are still running Android 2.3 (“Gingerbread”), which had its initial release back in 2010.
“The biggest issue is that around half of the devices out there likely won’t see an update. With Android’s fragmentation, a lot of devices are outdated and the carriers no longer push updates,” says Malwarebytes own Armando Orozco.
Bluebox plans to release technical details of the vulnerability this year during Forristal’s Black Hat 2013 talk. In the meantime, Android users should continue to take extra precaution when installing apps, ensuring they are downloaded from trusted publishers.
_______________________________________________________________________________
Joshua Cannell is a Malware Intelligence Analyst at Malwarebytes where he performs research and in-depth analysis on current malware threats. He has over 5 years of experience working with US defense intelligence agencies where he analyzed malware and developed defense strategies through reverse engineering techniques. His articles on the Unpacked blog feature the latest news in malware as well as full-length technical analysis. Follow him on Twitter @joshcannell









