Facebook awarded its highest bug bounty to date to a Brazilian Security Engineer Reginaldo Silva, yesterday.
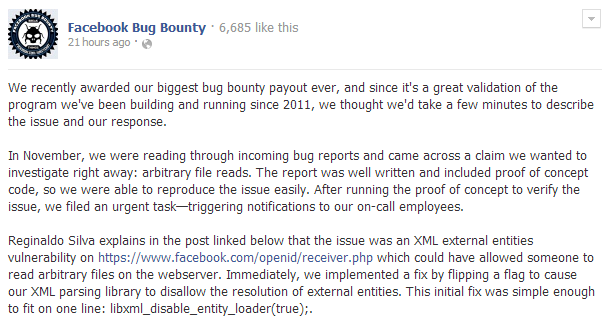
The bounty, an estimated total of $33,500, was awarded for disclosing an XML external entities vulnerability within a PHP page hosted on their servers.
“XXEs are very nice,” Silva, who specializes in Web Application Security, writes in his blog. “They allow you to read any files on the filesystem, make arbitrary network connections, and just for the kicks you can also DoS the server with the billion laughs attack.”
Silva discovered the vulnerability back in November and began the disclosure process with Facebook shortly after discovery.
However, when Silva first discovered the bug he wanted to wait on disclosing it to Facebook until he had a full Remote Code Execution (RCE) bug produced.
These type of vulnerabilities may lead to malware infections and therefore have higher payouts. Nonetheless, Silva reported the bug to Facebook and decided to try and escalate it to a RCE. However, when he had returned after a quick-lunch break, the bug was already patched.
“I was very impressed and disappointed at the same time,” Silva wrote in his blog. “But since I knew just how I would escalate that attack to a Remote Code Execution bug, I decided to tell the security team what I’d do to escalate my access and trust them to be honest when they tested to see if the attack I had in my mind worked or not.”
Facebook confirmed the vulnerability as a potential RCE bug in a statement in their blog yesterday.
“We discussed the matter further,” the statement said. “Due to a valid scenario he theorized involving an administrative feature we are scheduled to deprecate soon, we decided to re-classify the issue as a potential RCE bug.”
Congratulations to Silva for doing the right thing and disclosing this properly. Needless to say, any blackhat would be drooling for the opportunity to get a foothold into the social media giant with over 1 billion users.
For more details on Silva and his work on this bug, you can check out his writeup.
_________________________________________________________________
Joshua Cannell is a Malware Intelligence Analyst at Malwarebytes where he performs research and in-depth analysis on current malware threats. Follow him on Twitter @joshcannell









