The Sality Malware family has been around since 2003 and has undergone many changes since that time. However, the malware’s latest component might be one of the most interesting to date.
Discovered by researchers at ESET, Win32/RBrute.A is a Sality component capable of changing a router’s primary DNS server. Malware with this functionality has been seen in the past, the most notable probably being the simply named “DNSChanger” developed by Estonian hackers.
For those unfamiliar with DNS and what it does, it’s the protocol responsible for translating names to IP addresses. It is a very important part of how the internet itself operates, as directing users to the wrong place is not only annoying and inconvenient, but could expose them to malicious pages.
The ESET researchers go on to prove that, explaining how this Sality component redirects searches for “google” and “facebook” to rogue servers that distribute Sality, “providing a way for the Sality botnet’s operators to increase its size further by infecting other users behind this router.”
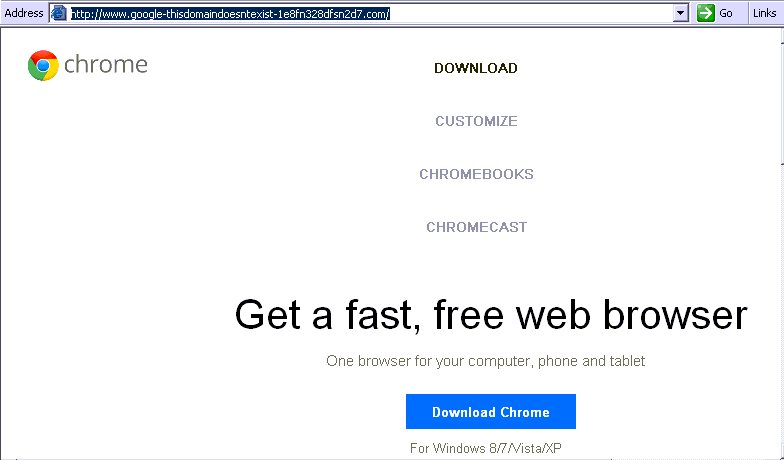
Fake Google Chrome download page (Image: ESET)
The malware targets routers using common usernames and passwords. At the time or reporting, ESET states the malware targets the following routers:
- Cisco routers matching “level_15_” in the HTTP realm attribute
- D-Link DSL-2520U
- D-Link DSL-2542B
- D-Link DSL-2600U
- Huawei EchoLife
- TP-LINK
- TP-Link TD-8816
- TP-Link TD-8817
- TP-Link TD-8817 2.0
- TP-Link TD-8840T
- TP-Link TD-8840T 2.0
- TP-Link TD-W8101G
- TP-Link TD-W8151N
- TP-Link TD-W8901G
- TP-Link TD-W8901G 3.0
- TP-Link TD-W8901GB
- TP-Link TD-W8951ND
- TP-Link TD-W8961ND
- ZTE ZXDSL 831CII
- ZTE ZXV10 W300
DNS-changing malware can obviously be a scary thing, especially since fake webpages located on rogue servers are easily crafted and appear original. While ESET has only reported on fake download pages for Google Chrome, it seems likely that this Sality component will continue to advance, possibly in the form of fake login pages that steal user credentials.
To protect yourself from Sality and other advanced malware, ensure you have a good Antivirus software installed on your PC that’s updated frequently. Malwarebytes also offers a wide range of products that provide protection from malware; to find out more, check out our products page.
To view the full analysis of Sality’s DNS Changer, check out their blog.
_________________________________________________________________ Joshua Cannell is a Malware Intelligence Analyst at Malwarebytes where he performs research and malware analysis. Twitter: @joshcannell