Traditionally, malware attacks as we have always known them are files written to disk in one form or another that require…
Tag: windows
Free tools: Internet traffic monitoring
Are you an amateur analyst or security enthusiast looking for free tools to do some basic Internet traffic monitoring? You’ve come…
Solution Corner: Malwarebytes Incident Response
Unless you’ve been stuck at a fiery music festival, I don’t need to tell you the threat landscape is constantly evolving…
The worm that spreads WanaCrypt0r
Something that many security researchers have feared has indeed come true. Threat actors have integrated a critical exploit taking advantage of…
Adware the series, part 3
In this series of posts, we will be using the flowchart below to follow the process of determining which adware we are dealing…
ShadowBrokers releases more stolen information
ShadowBrokers shocked the security world again today by releasing another cache of exploits, files, and operational documents purportedly stolen from Equation…
Explained: Environmental variables
Sometimes when you are looking for instructions to troubleshoot software issues or adapt software to your liking and you are looking…
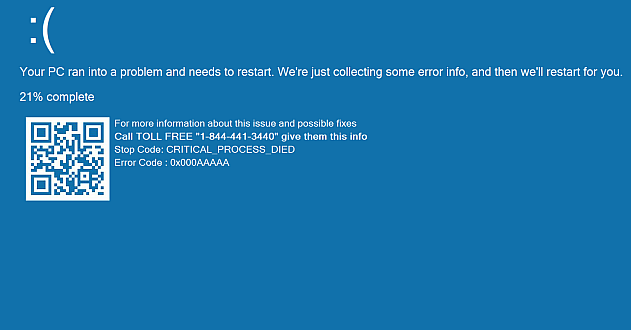
A closer look at a tech support screen locker
In this blog post, we are going to take a closer look at some of the code that the most predominant…
iPad error? Windows fakeout
This “You have a virus” page caught my eye today, drawing as it does on multiple tech sources to try (and sort…
Windows AppLocker: An Introduction
Windows AppLocker is a feature that was introduced in Windows 7 and Windows Server 2008 R2 as a means to limit…